BIT CRACKER
1. Initialization & First Boot
When booting the Bit Cracker operator interface for the first time, terminals pass through an initialization sequence designed for core security and network compliance.
Based on global network compliance, operators undergo a Security Clearance check (<16 or 16+ cycles) and accept GDPR/COPPA directives to configure targeted telemetry and data privacy firewalls.
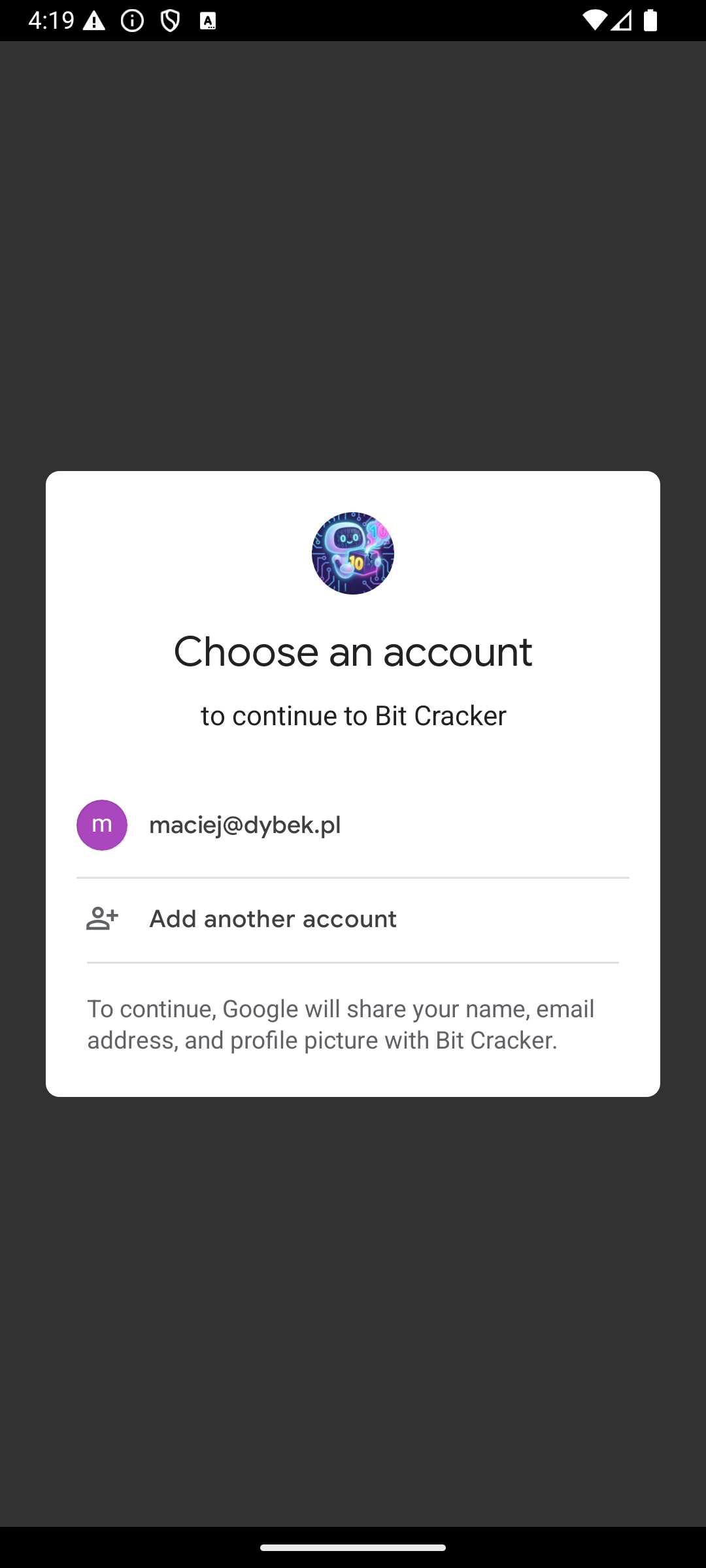
Authentication Protocol
Operator uplink interface.
- Ghost profile initialized by default.
- Simple skip/close for untraceable mode.
- Global Node (Google) uplink for mainframe synchronization.
- Link identity to transfer stats between terminals.
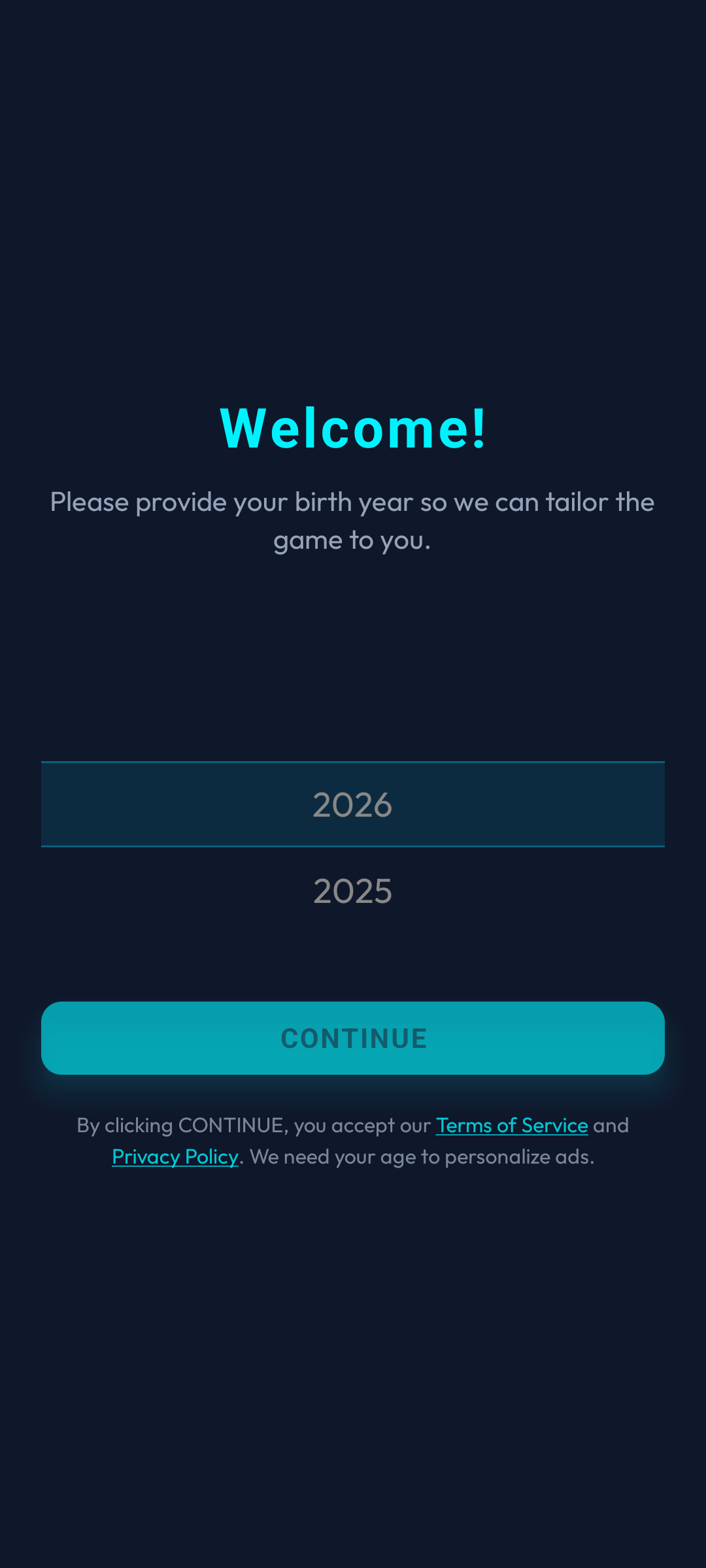
Security Directive (COPPA)
Initial phase of the network verification protocol.
- Exact cycle logs (birth dates) are purged.
- Determines telemetry and ad routing (<16 vs 16+).
- Data isolated in local terminal memory (AsyncStorage).
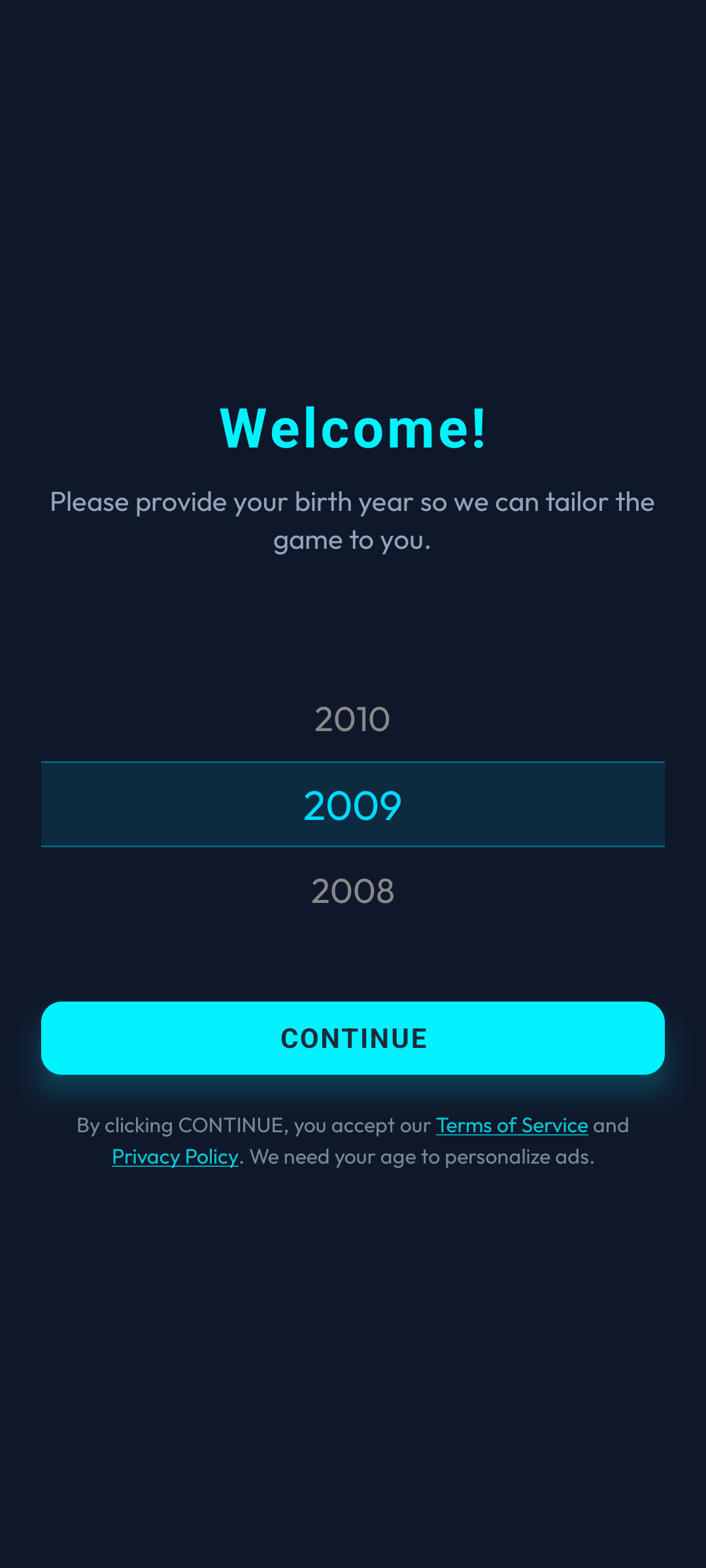
Cycle Confirmation
Final cycle confirmation protocol.
- Locks in the verified birth cycle.
- Prevents operational misclicks.
- Proceeding implies acceptance of network privacy firewalls.
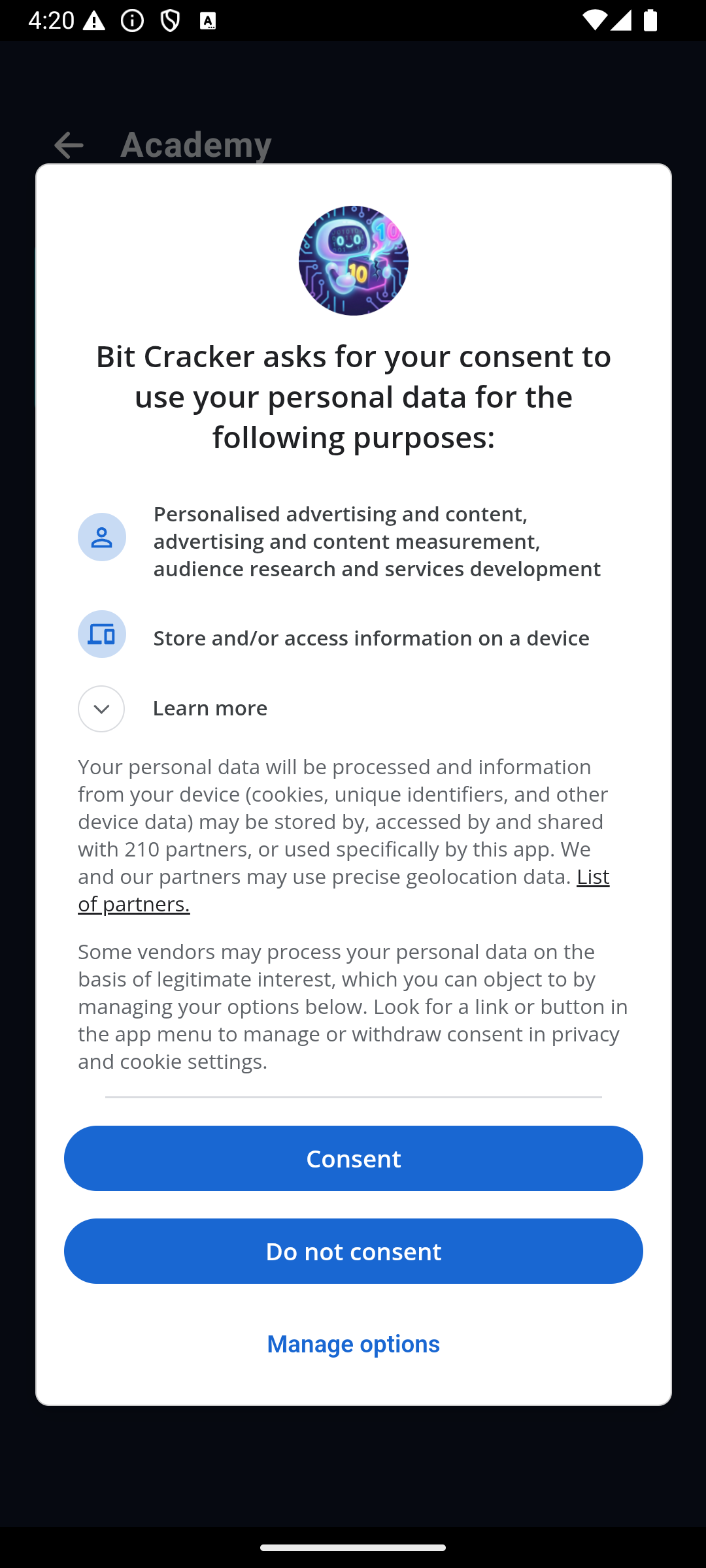
GDPR Consent
European data tracking compliance.
- Displayed exclusively to cleared adults (16+).
- Routed via AdMob UMP transmission protocols.
- Requests authorization for targeted data streams.
- Directives can be altered later in the Operator Profile.
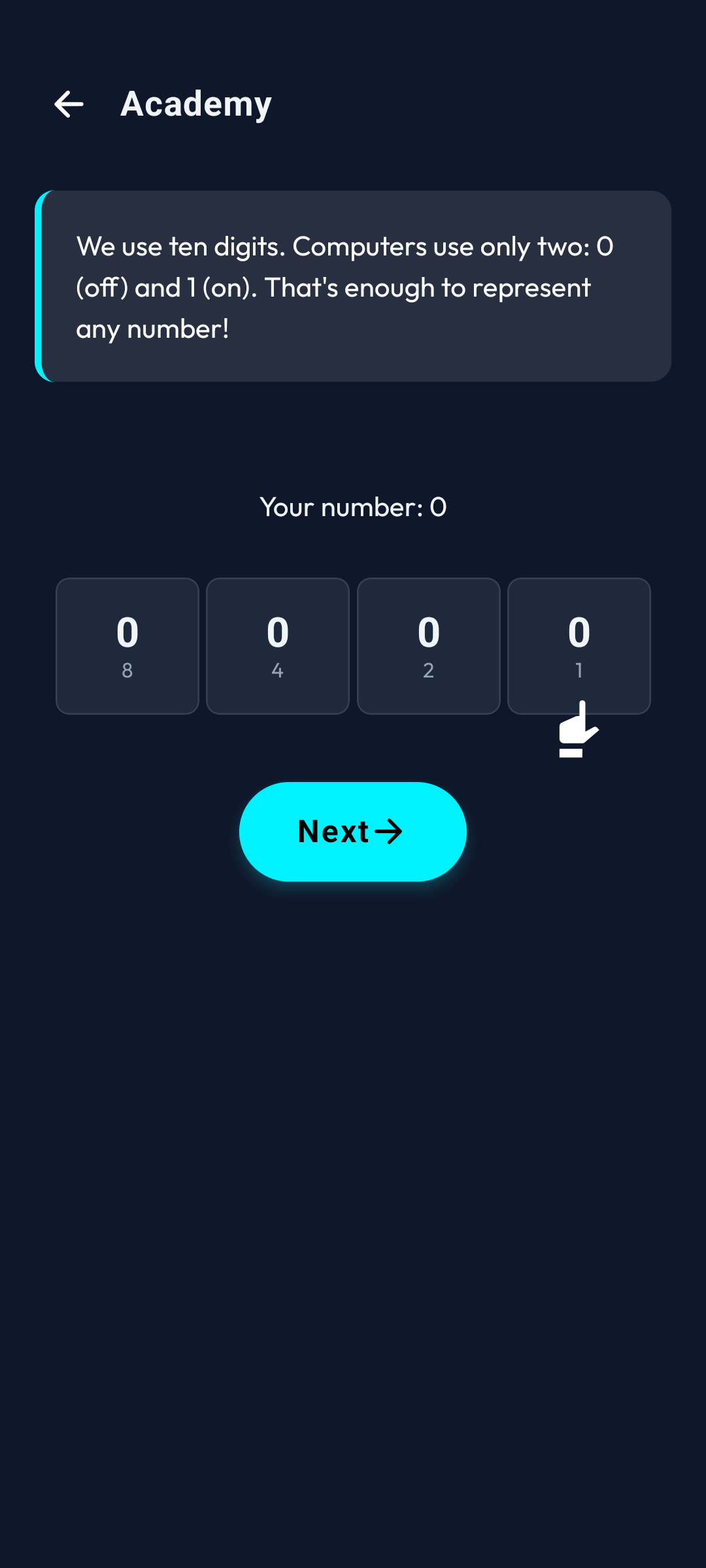
2. The Academy
Before executing live mainframe challenges, operators must train in the Academy. The simulation contains interactive modules explaining binary logic, data bits, and the operational switches essential for mastering core system overrides.
Academy Intro
Welcome to the core logic simulator.
- Zero energy drain.
- Downloads Bit Cracker operational lore.
- Mandatory broadcast on first boot.
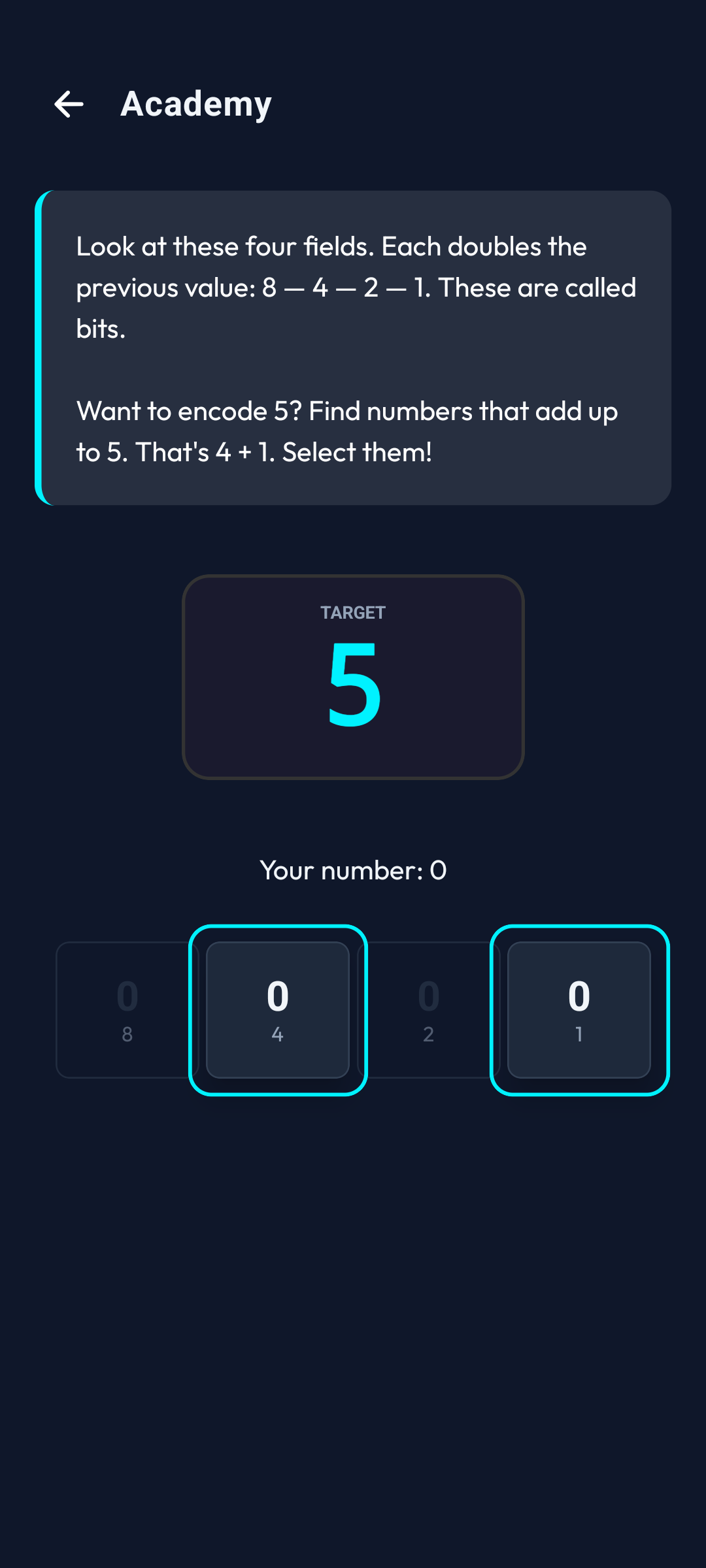
Binary Protocol
Interactive data logic guide.
- Calibrates base-2 numeral processing.
- Maps bit values (1, 2, 4, 8...).
- Required tactical knowledge for Bit Invader.

Clearance Granted
End of the interactive diagnostic.
- Grants the 'Bit Master' clearance badge.
- Unlocks core mainframe access.
- Archive access available via the Main Interface.
3. Operator Interface (Central Node)
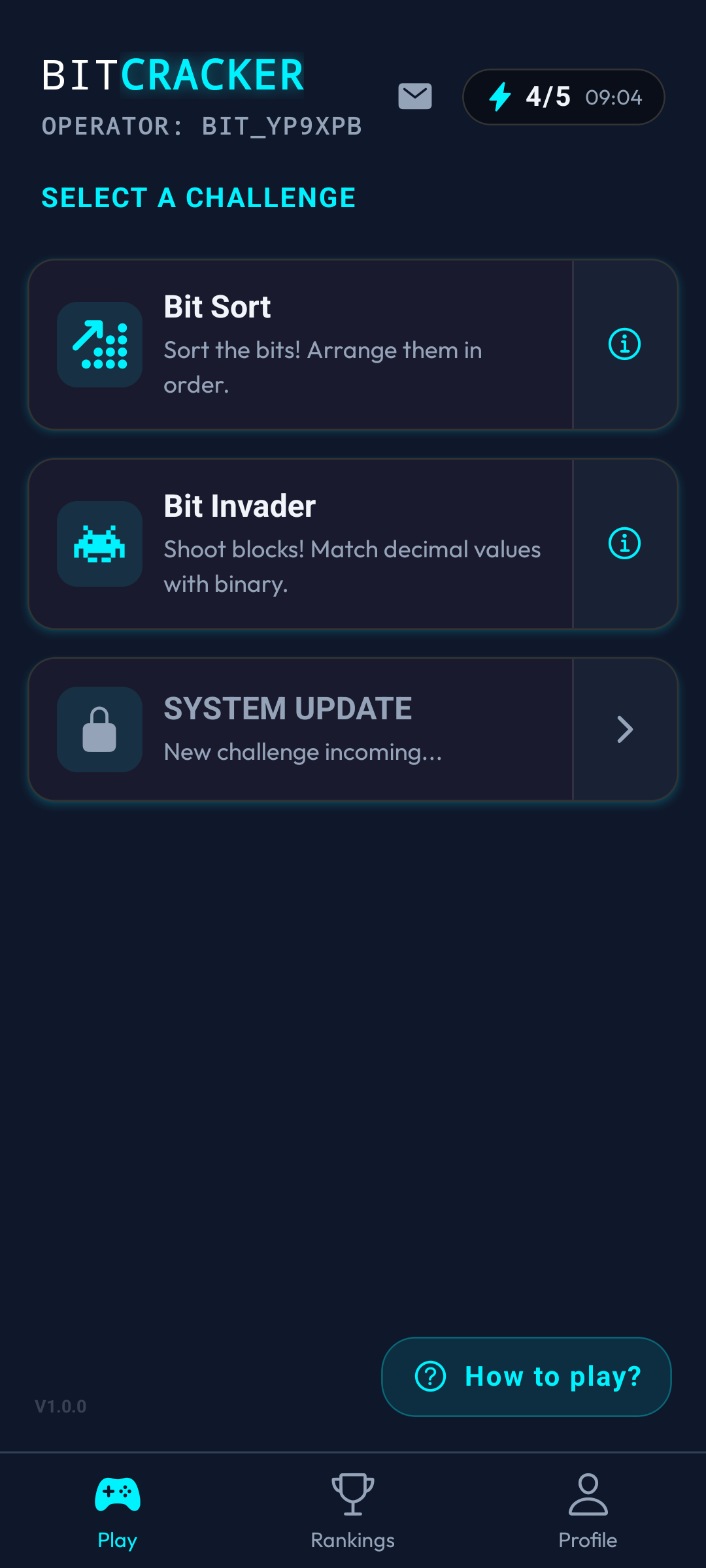
The primary interface acts as the central command node. Operators can initiate the Bit Sort and Bit Invader execution sequences, monitor core energy (System Status), decrypt internal transmissions, and intercept update signals from the server architecture.
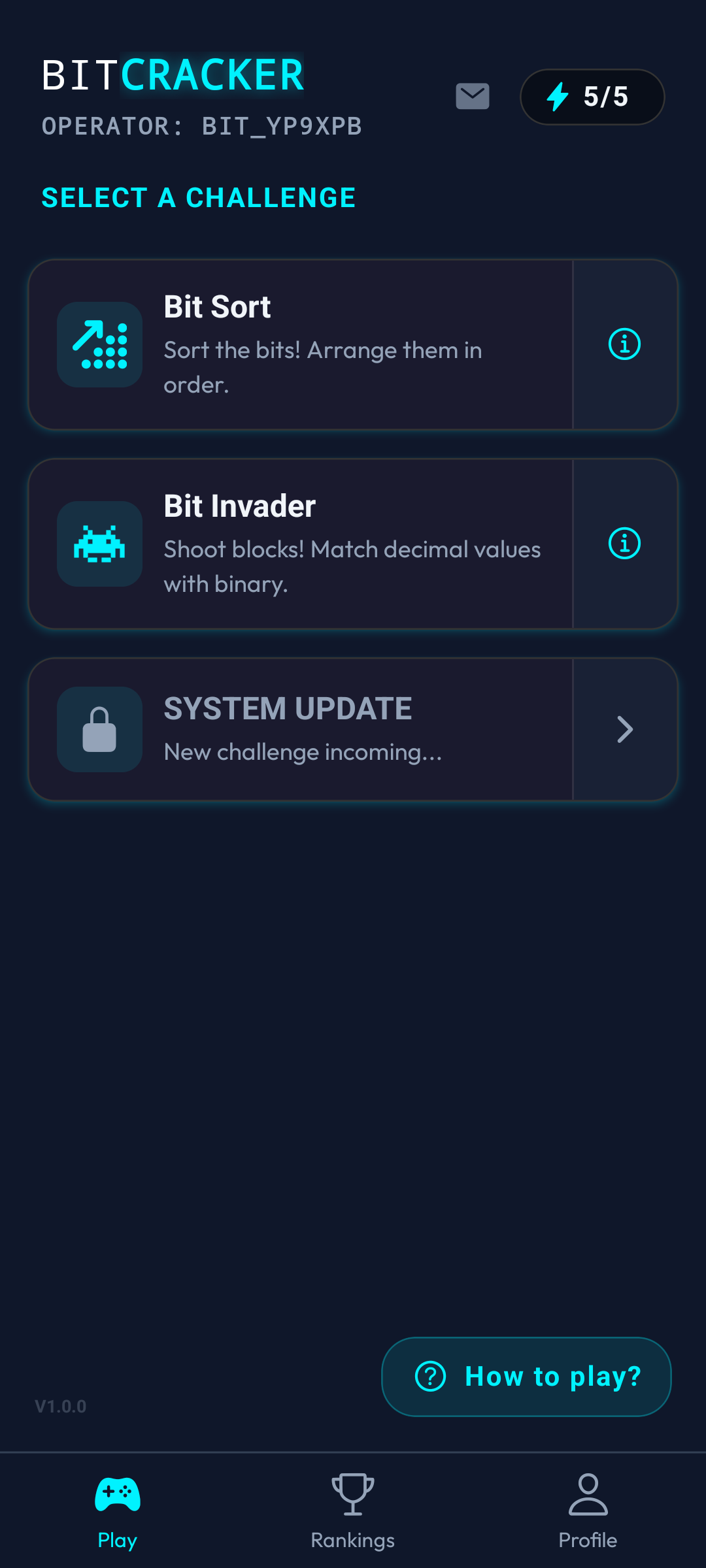
Command Node
The central hub of the terminal.
- Displays the active Callsign (e.g., BIT_X9).
- Initiates Bit Sort and Bit Invader sequences.
- Monitors current energy levels in the header.
- Tapping the energy node opens System Diagnostics.
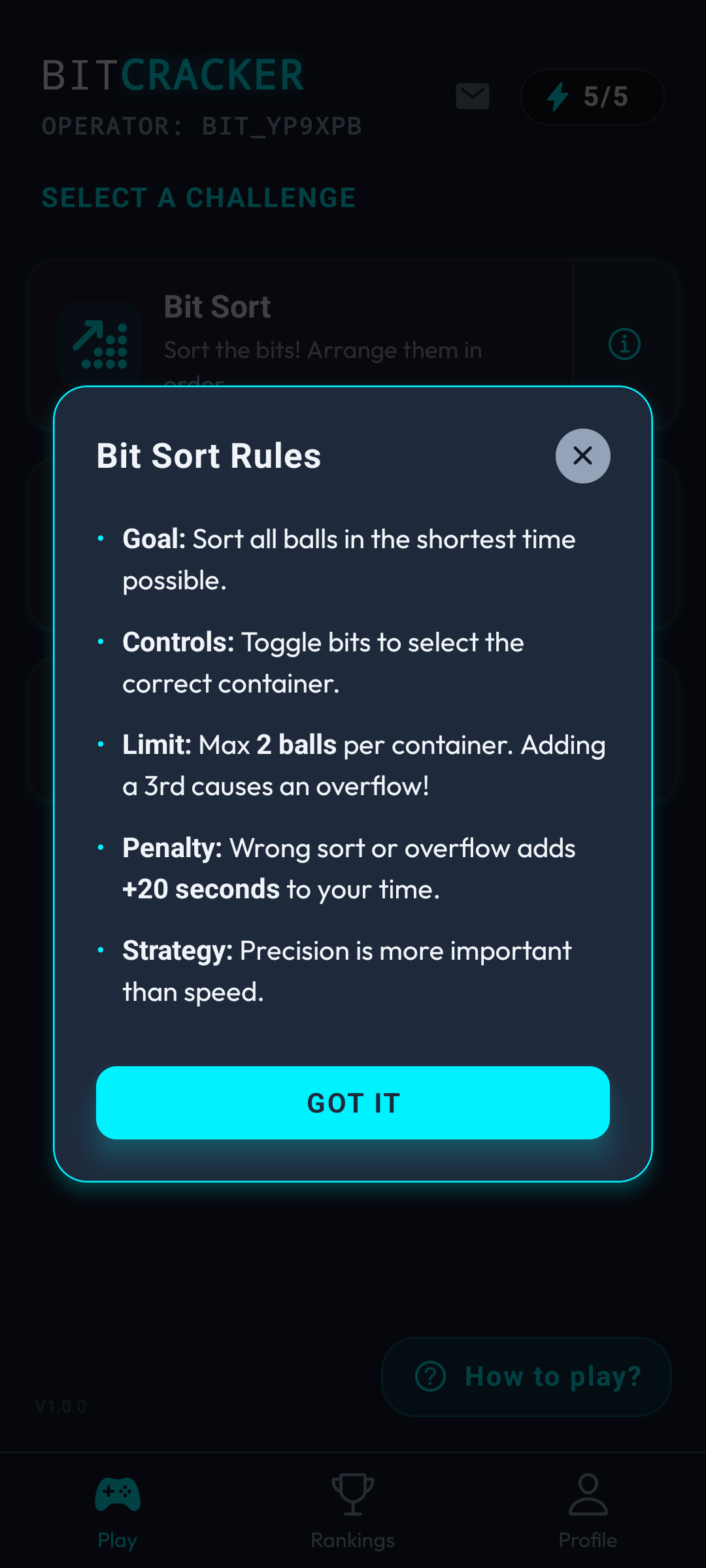
Execution Rules
Access the info node to read tactical parameters.
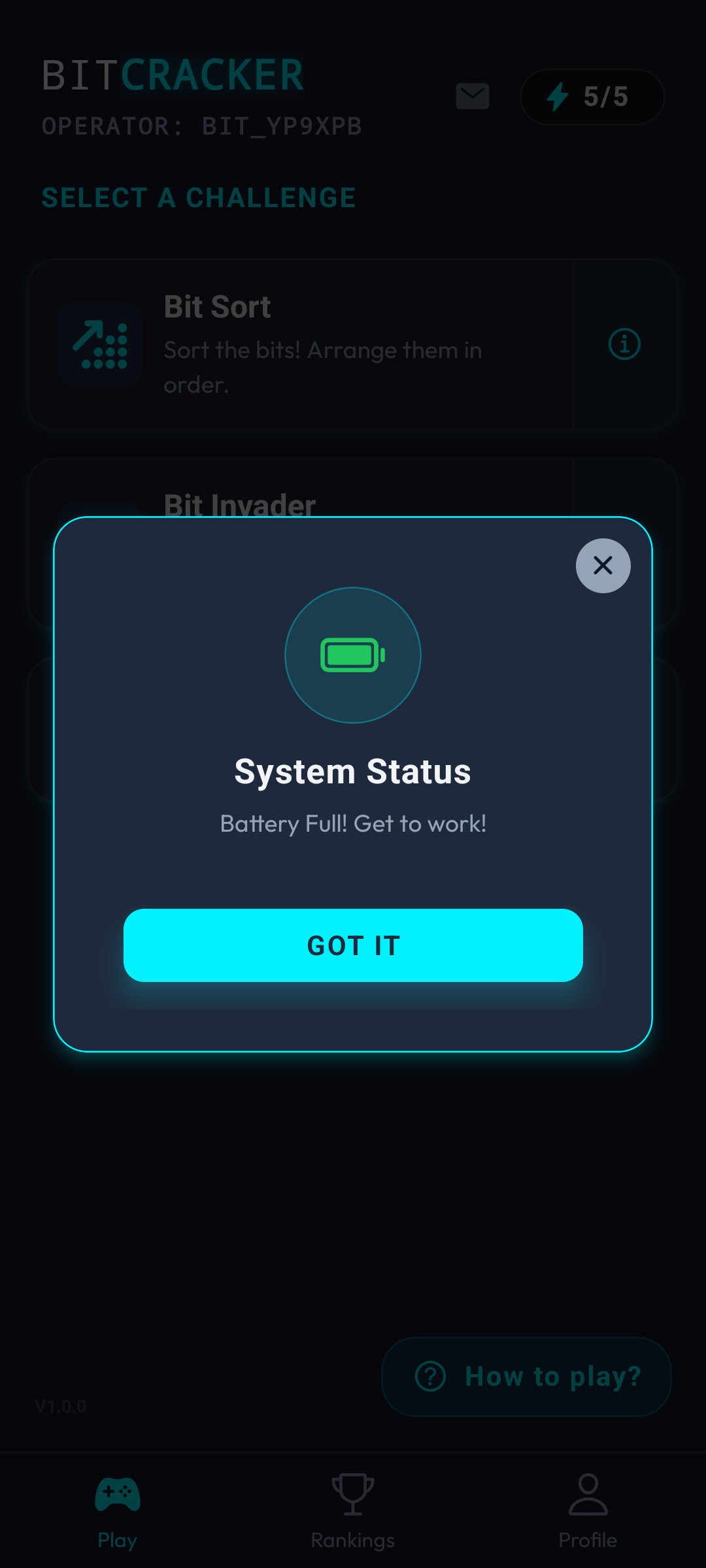
Core Charged
Maximum operational capacity reached.
- Energy grid is fully restored.
- Terminal is ready for execution.
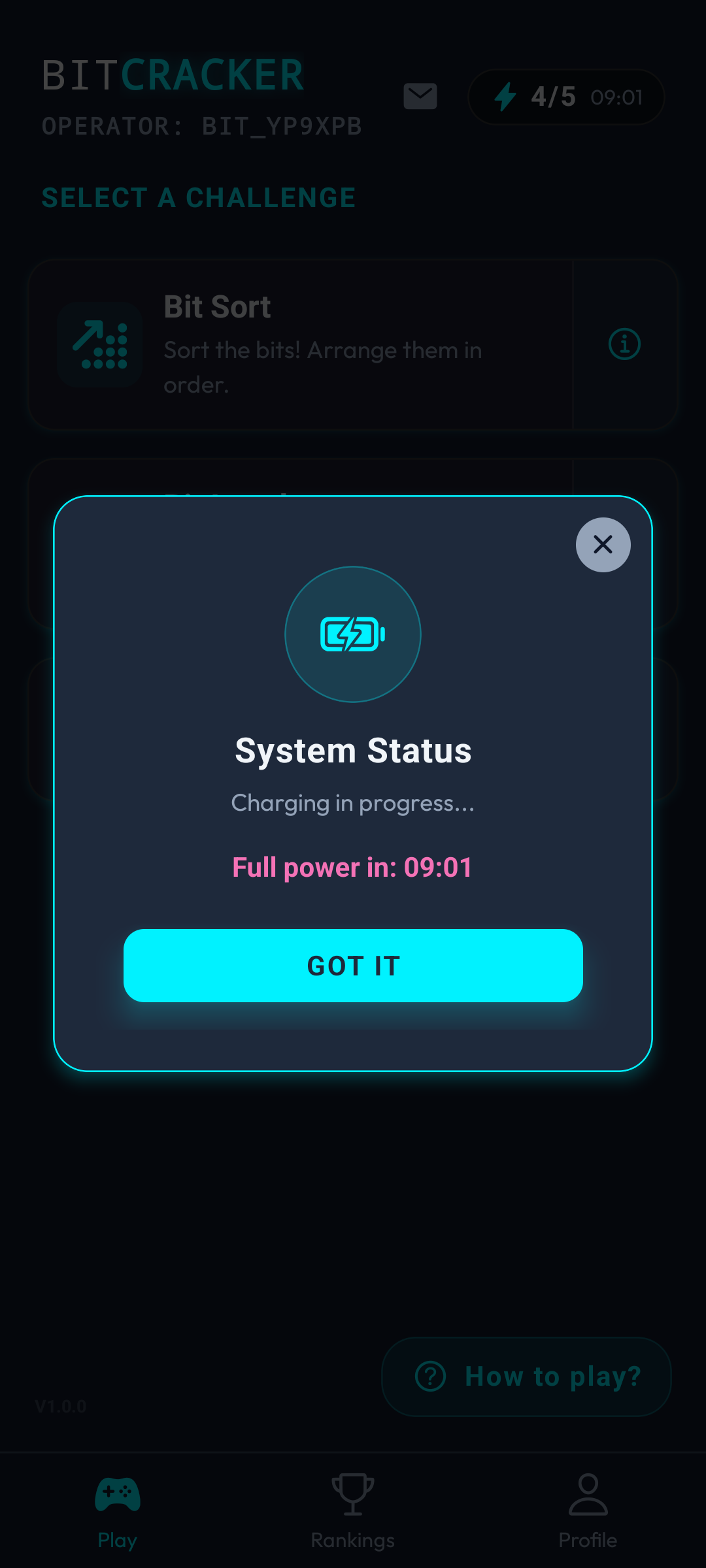
Energy Monitor
- Maximum grid capacity: 5 units.
- Requires 1 unit per execution sequence.
- Displays countdown to next recharge cycle.
- Standard cycle: 10 minutes per unit.
Ad-Uplink Recovery
Commercial broadcast intercept.
- Process an Ad broadcast to instantly restore energy.
- Overrides the standard 10-minute cycle.
- Simulation Mode is available as a fallback.
Display Adaptation
Dynamic hardware orientation.
- Full layout functions in portrait matrix.
- Full layout functions in landscape matrix.
- Calibrated across all operational screens.
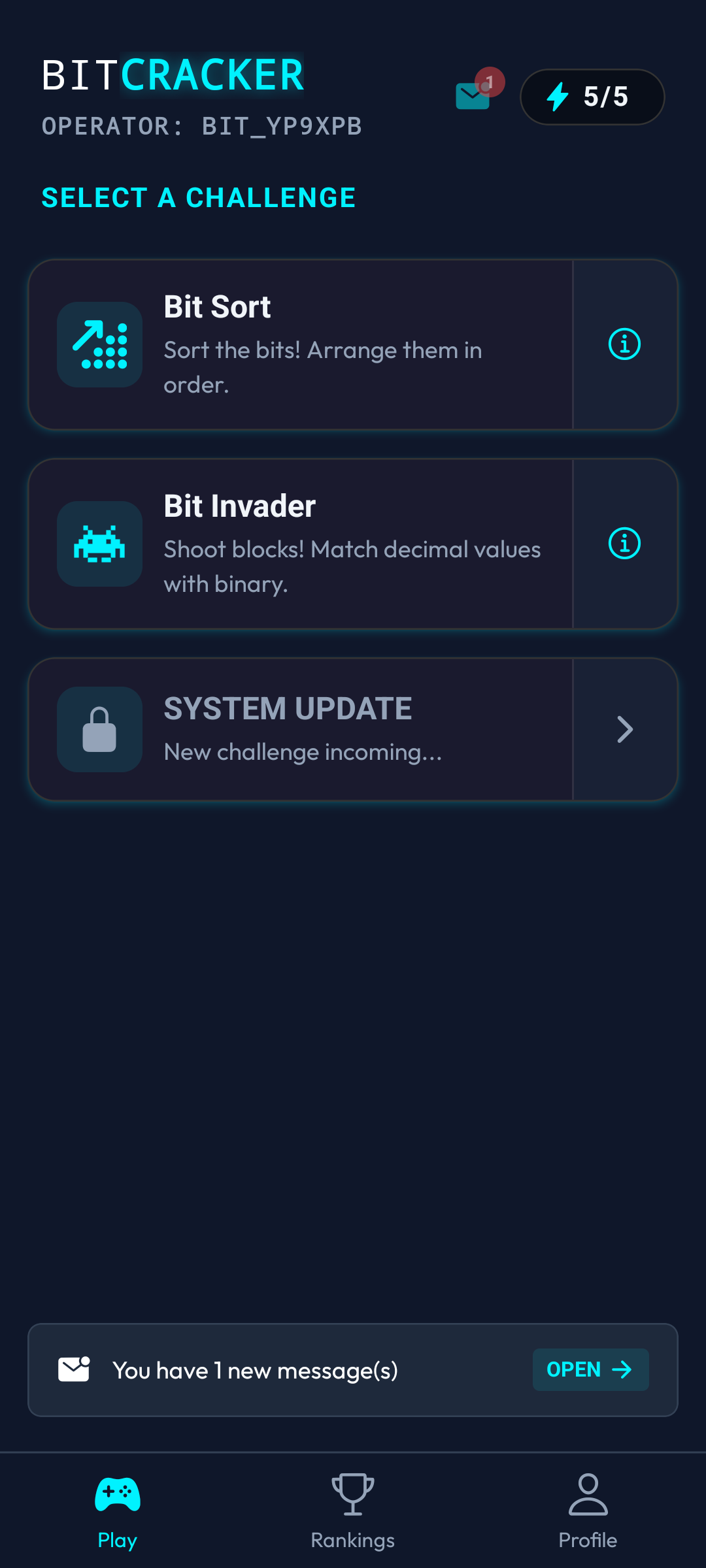
Transmission Alerts
Internal alert protocol for mainframe communications.
- Red flag indicates unread packets.
- Selecting the flag or bottom alert initiates decryption.
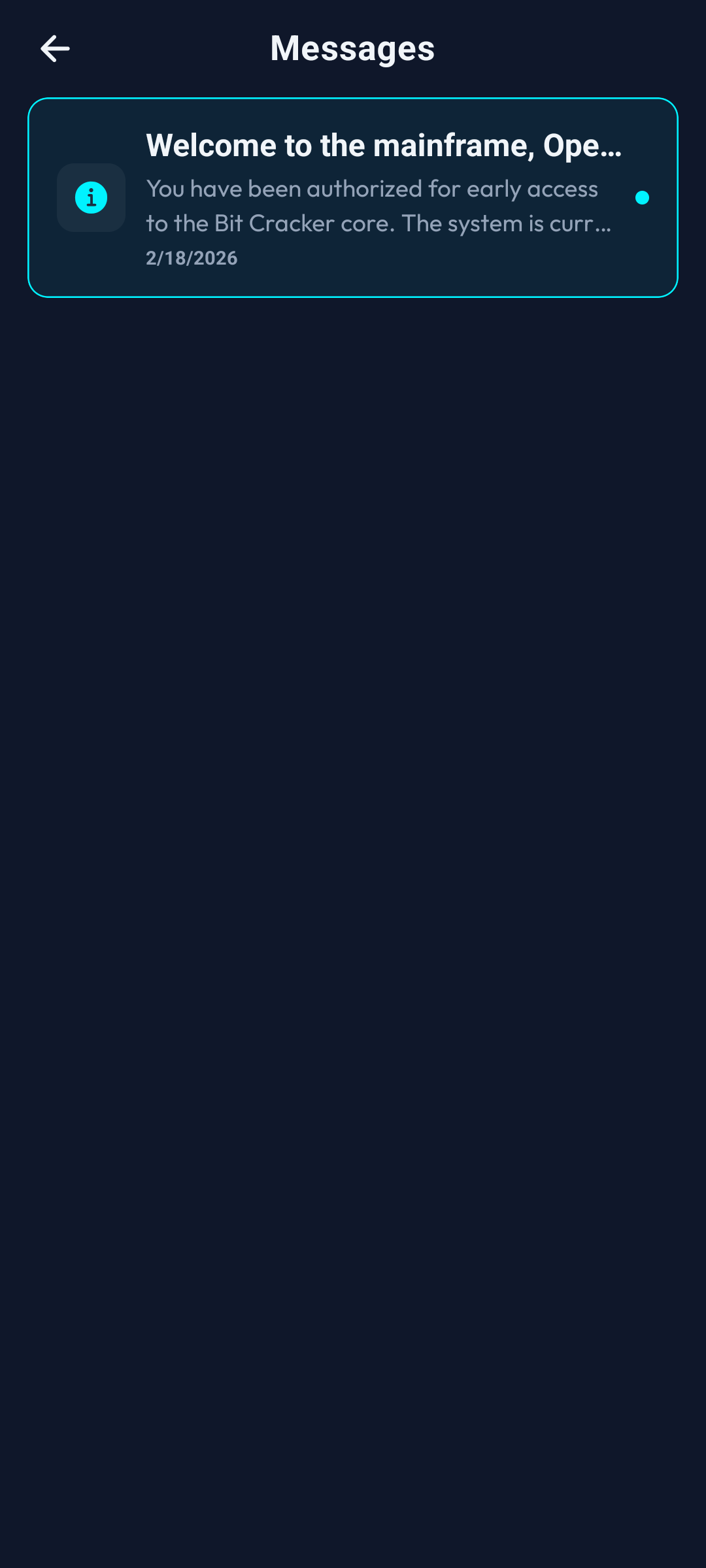
Secure Inbox
Registry of decrypted and encrypted packets.
- Select a packet to read raw data.
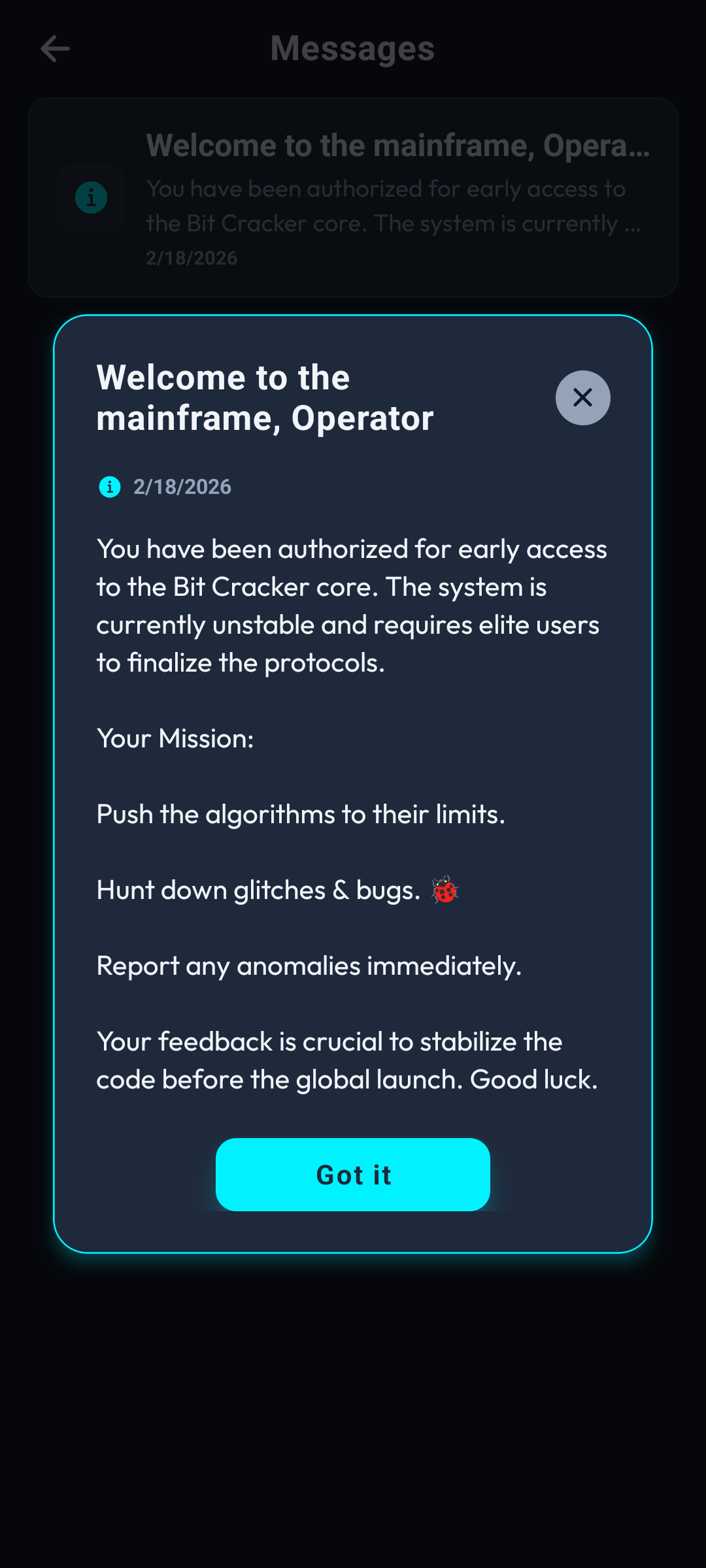
Packet Details
Full payload of an internal mainframe broadcast.
- Supports i18n linguistic conversion.
- Can contain encoded visual assets.
- Dismissal instantly flushes UI alert flags.
System Waitlist & Broadcasts
Operators can request clearance for experimental features via the System Signal uplink to be placed on an elite deployment waitlist.
Enroll in Deployment
Initialize subscription for tactical alerts.
- Execute 'SYSTEM UPDATE' in the command hub.
- Begins the encrypted enrollment sequence.
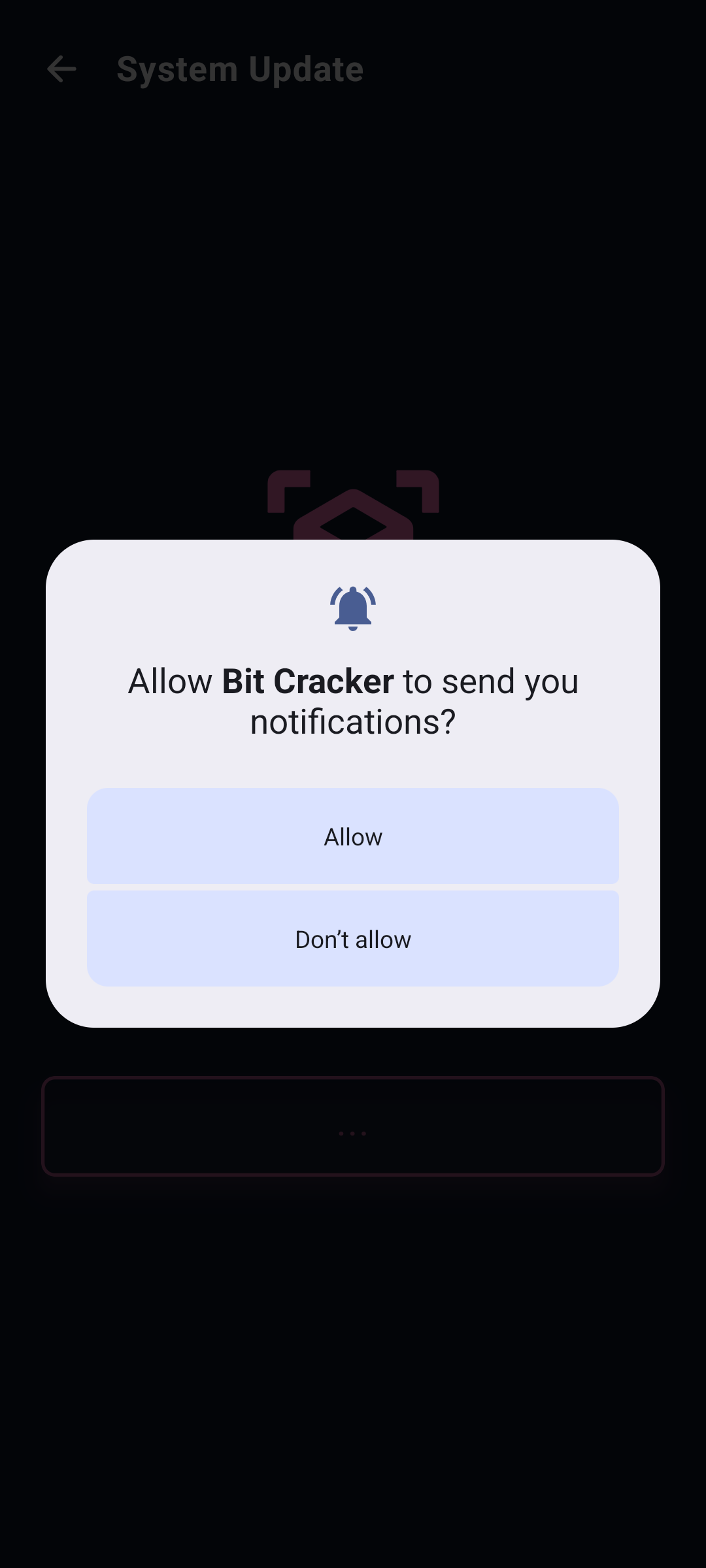
Enable Broadcasts
Authorize OS-level system alerts.
- Allow the terminal notification override.
- Enables real-time deployment of game patches.
- Crucial for the waitlist signal ping.
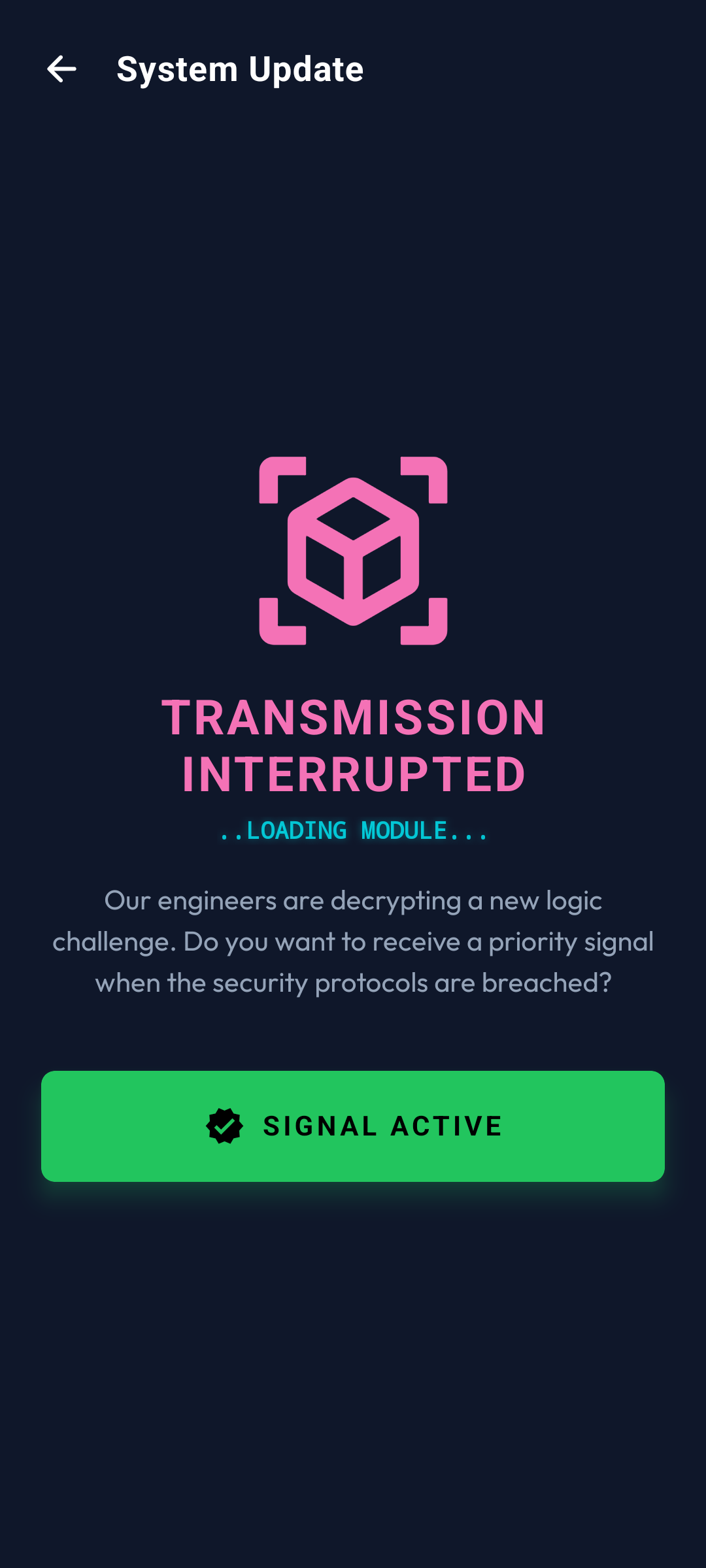
Signal Locked
Clearance granted for incoming architectures.
- You will receive push pings for new builds.
- Validation of waitlist registry.
- Automated alerts when dark zones are activated.
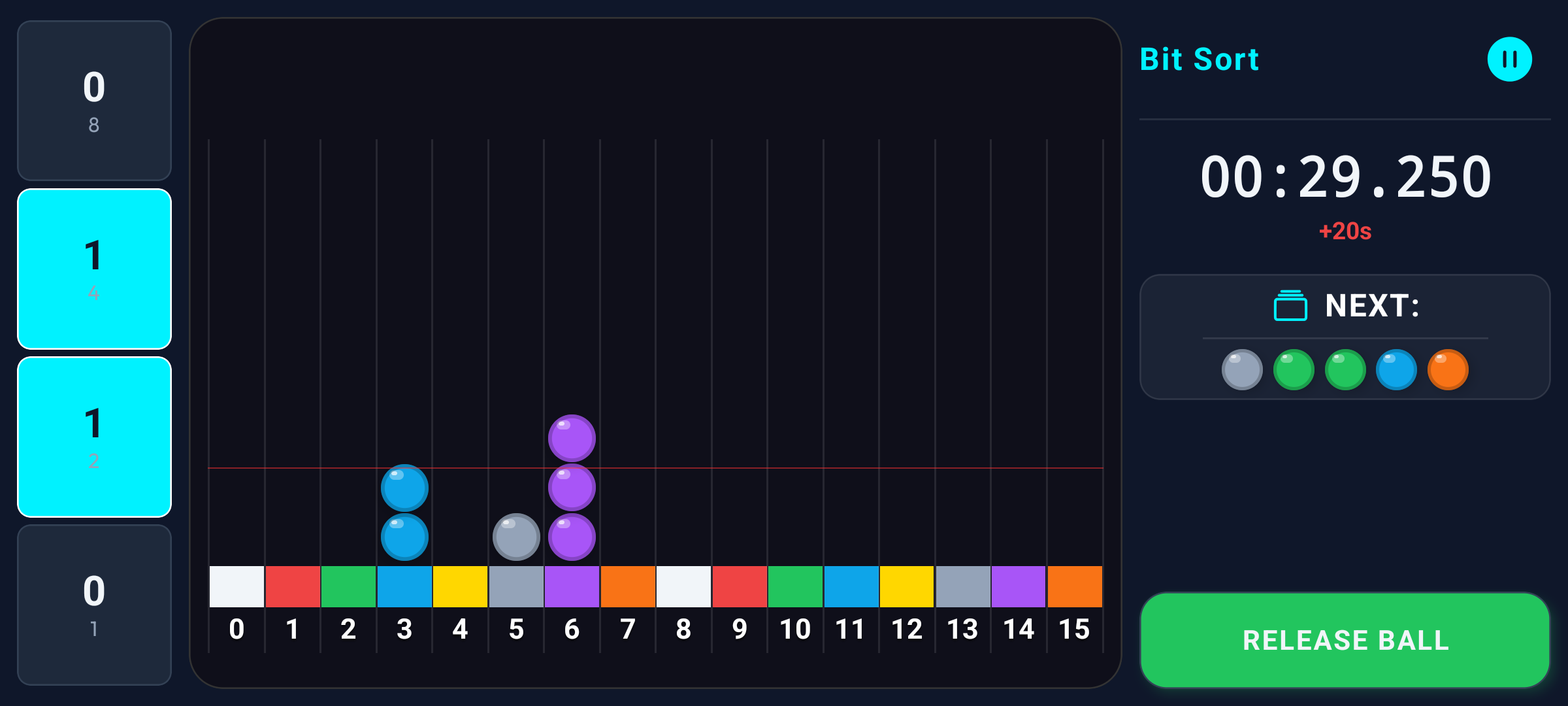
4. Execution: Bit Sort
A tactical logic module engineered to train binary processing speed. Operators must route falling data spheres into precise decimal buffers by manipulating truth-value logic gates (bits: 0/1).
Security Levels
| Level | Buffers | Bits | Tactical Aids |
|---|---|---|---|
| LEVEL 1 (EASY) | 8 (0-7) | 3 | Full trajectory paths, decimal container tags, basic bit overlays. |
| LEVEL 2 (MEDIUM) | 16 (0-15) | 4 | Partial decimal tags, trajectory paths cloaked. |
| LEVEL 3 (HARD) | 16 (0-15) | 4 | Power notation (2ⁿ) only, zero decimal assistance. |
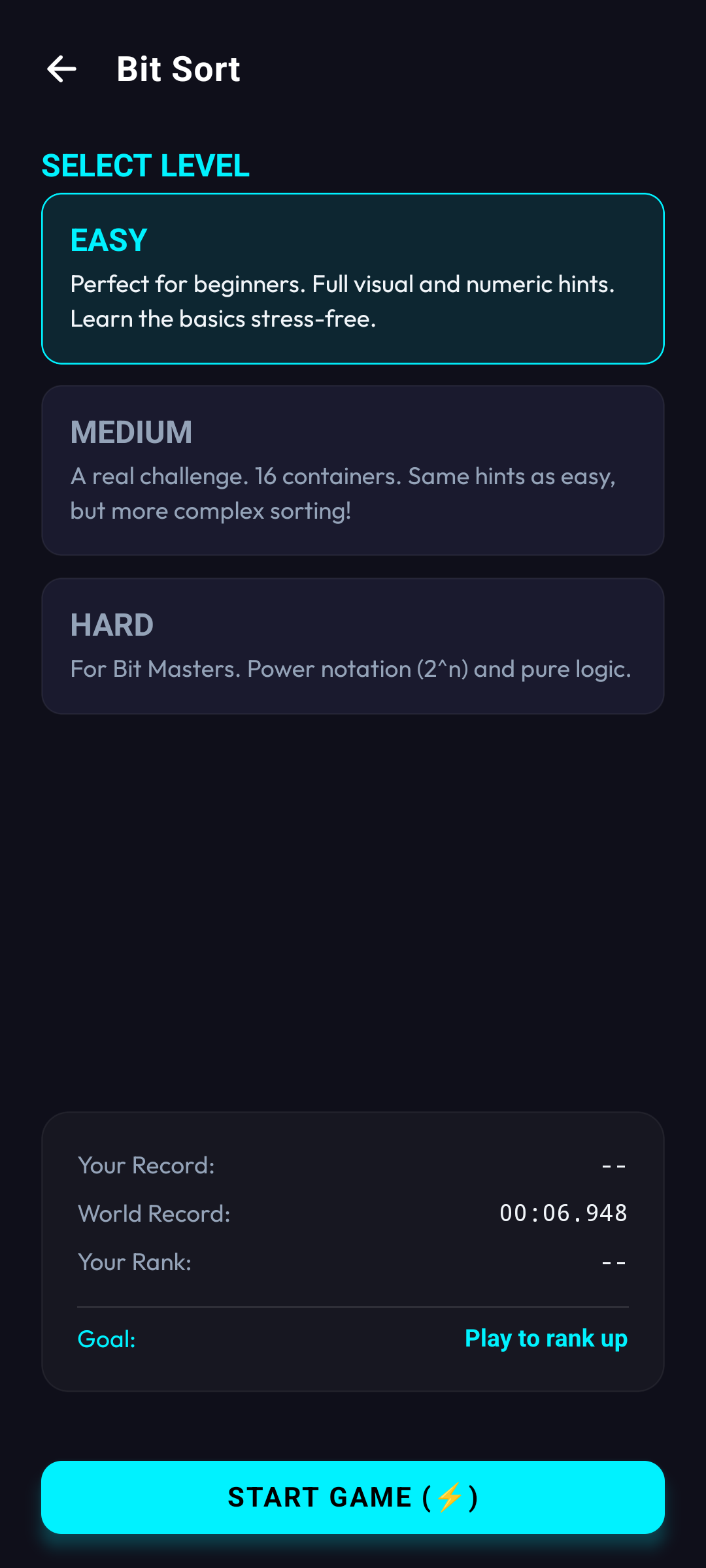
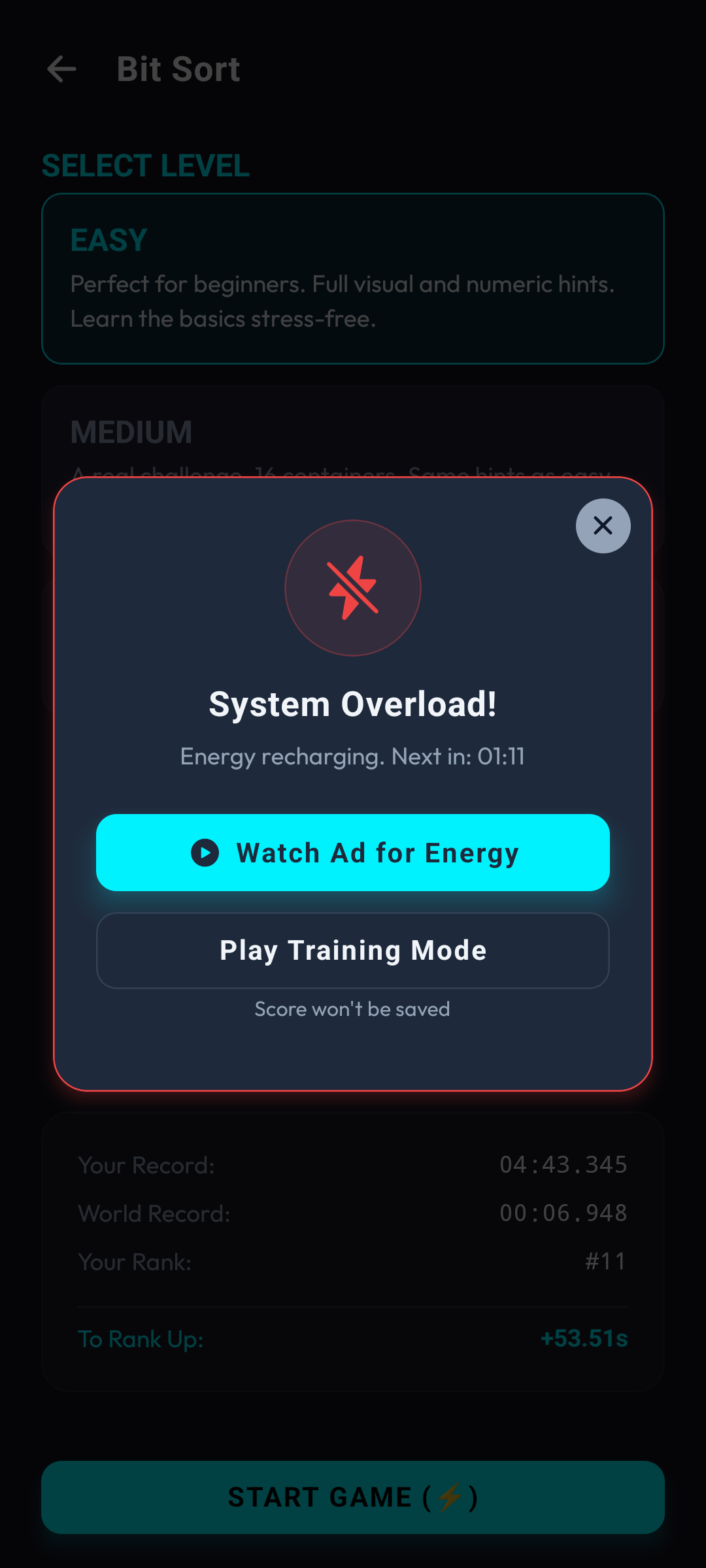
Security Level Setup
Pre-execution parameter selection.
- Select between 3 operational levels.
- LEVEL 1: 3 bits, full tactical overlays.
- LEVEL 2: 4 bits, partial overlays, cloaked paths.
- LEVEL 3: 4 bits, raw power notation (2ⁿ) only.
- Consumes 1 Energy unit to INITIATE.
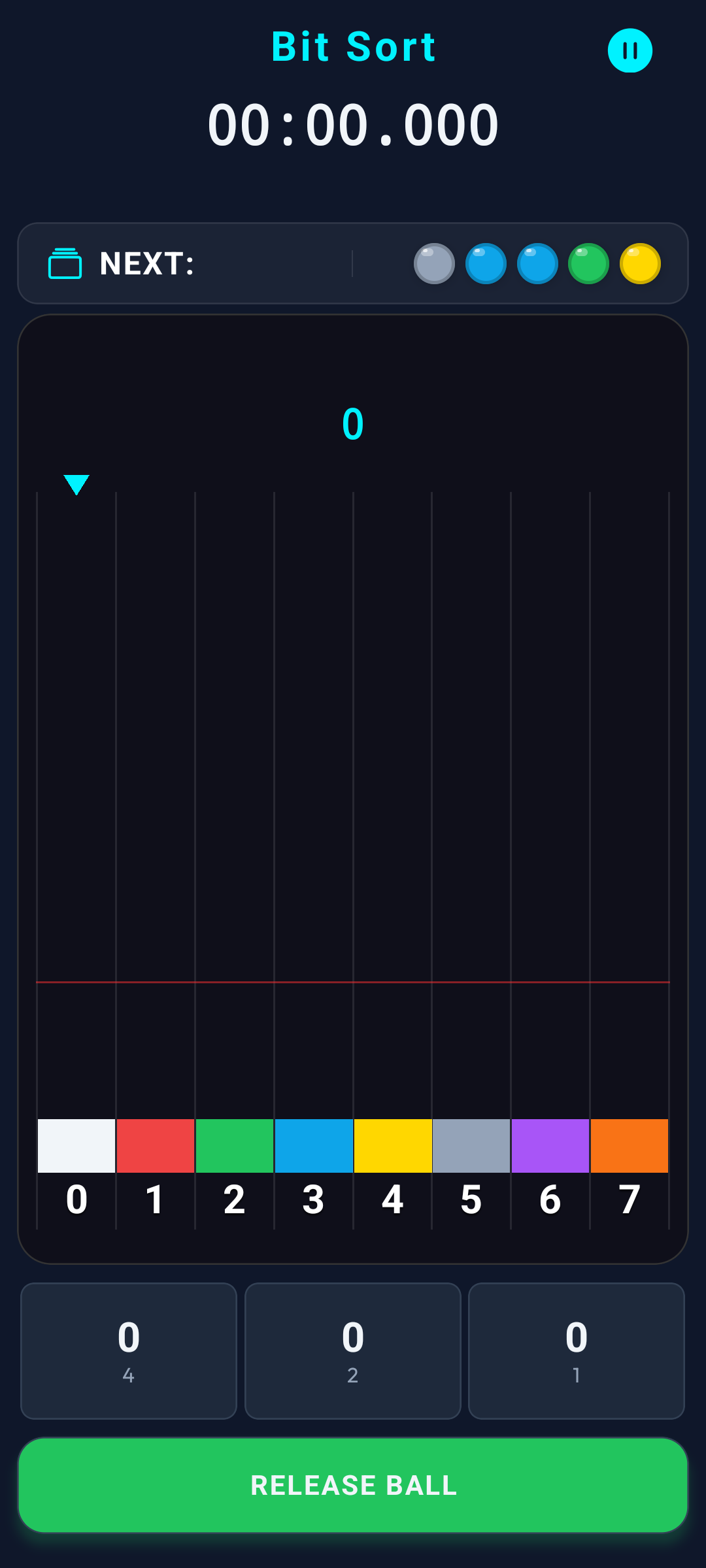
LEVEL 1 Execution
Baseline sorting parameters.
- 8 Buffers (0-7), 3 active logic gates.
- Visible trajectory streams.
- Decimal tags displayed on all target nodes.
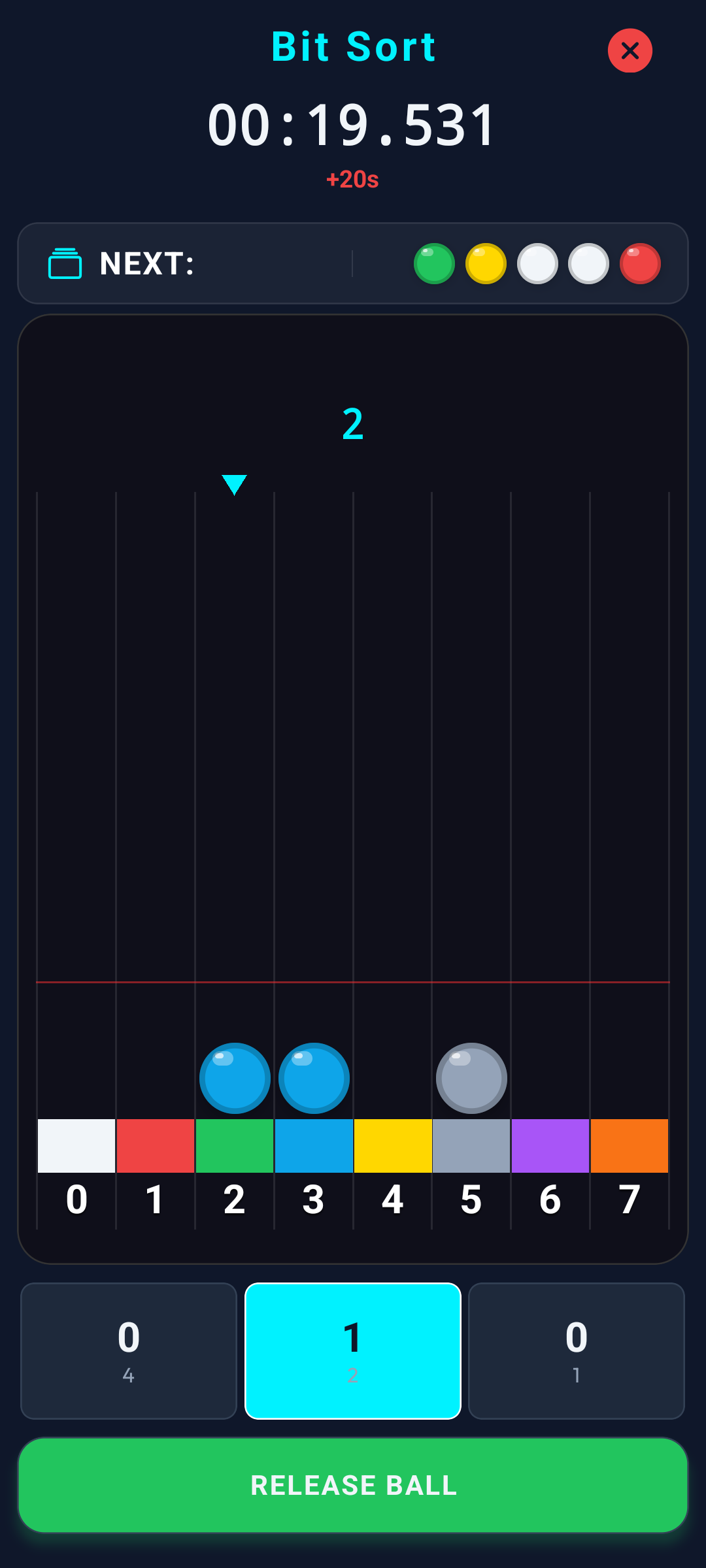
Violation Protocol
Routing errors trigger latency penalties.
- Invalid buffer routing injects +20s latency.
- Triggered by incorrect node or core overflow.
- Red limit line displays strict node capacity.
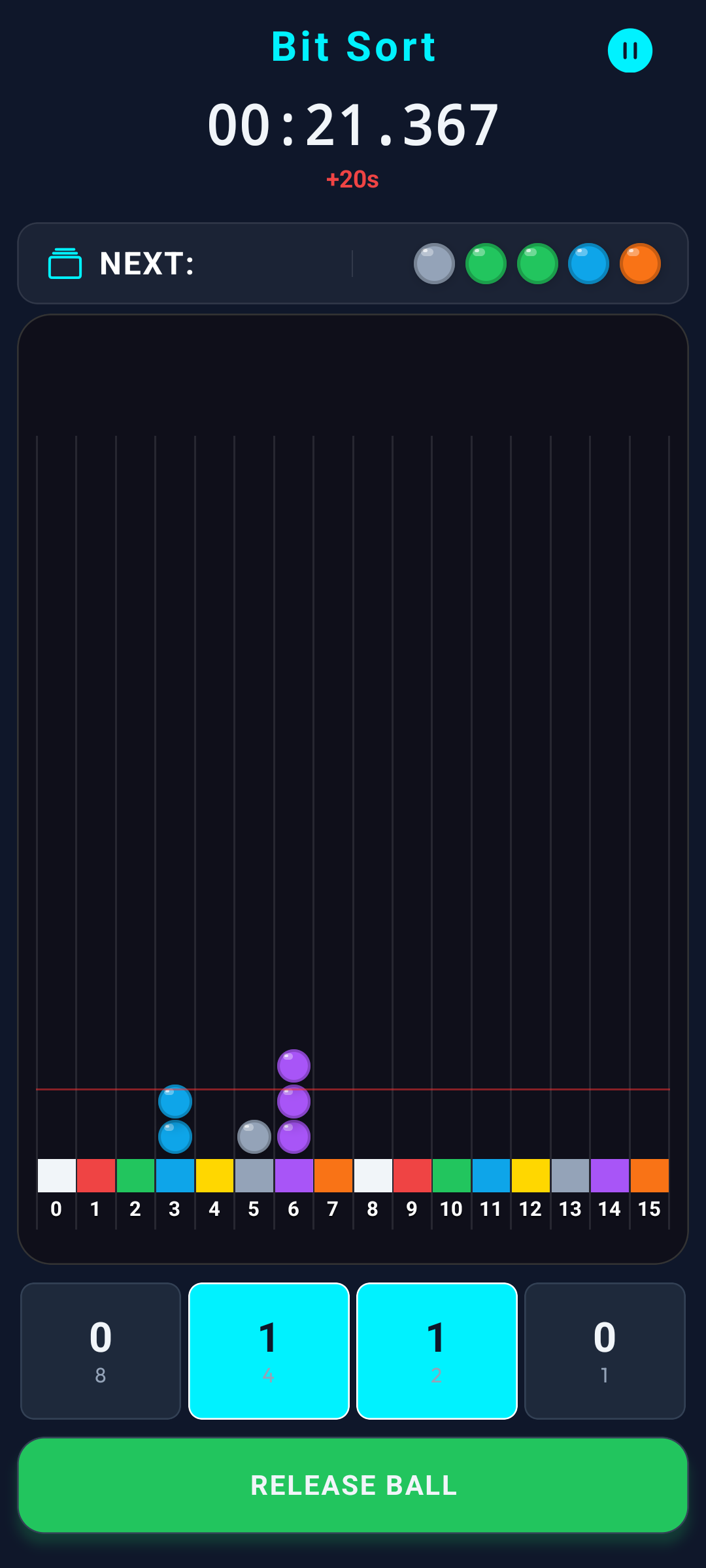
LEVEL 2 Execution
Intermediate security challenge.
- 16 Buffers (0-15), 4 active logic gates.
- Trajectory streams are cloaked.
- Partial decimal tags under logic switches.
- Selected blocks possess dual buffers (4 capacity).
- Red capacity limit requires strict monitoring.
- Spamming data causes catastrophic overflow.
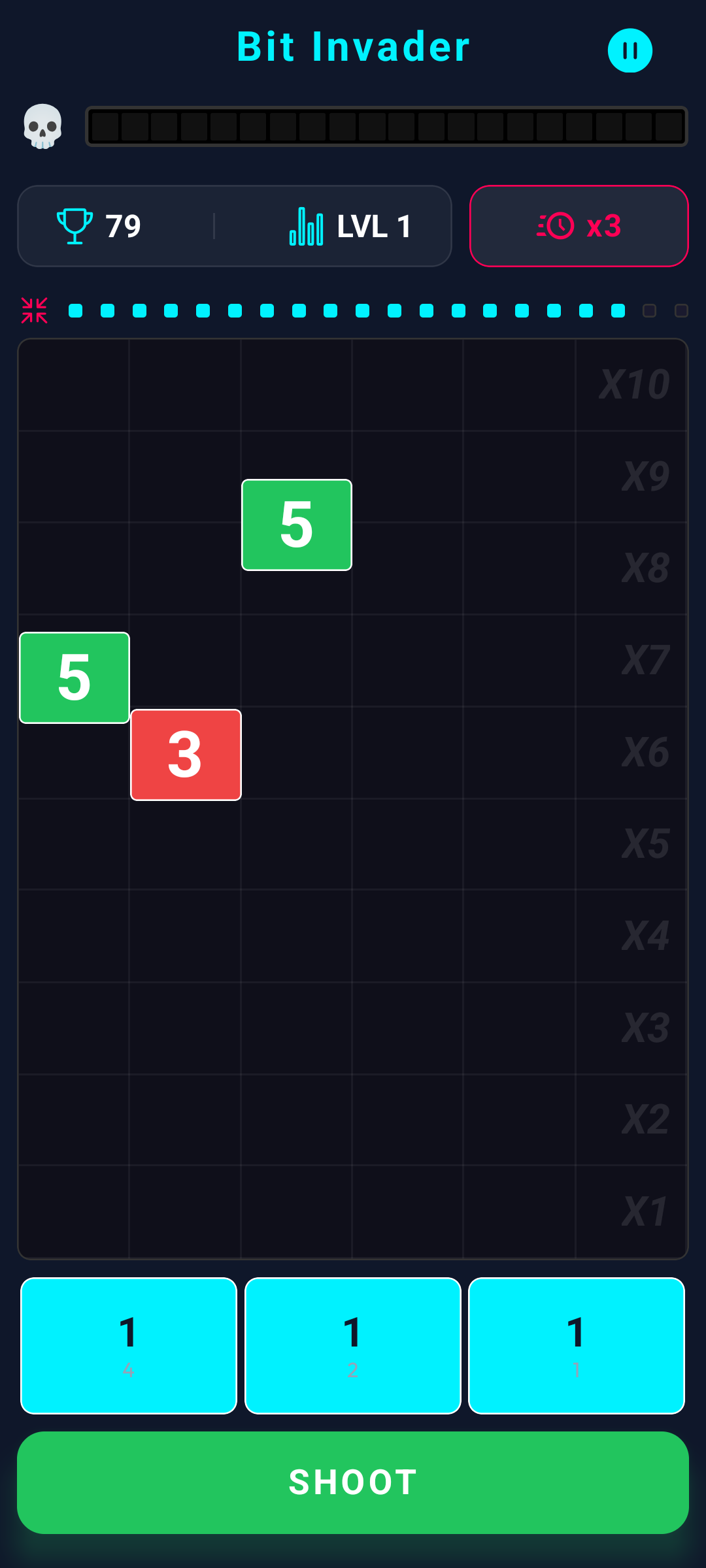
5. Execution: Bit Invader
A critical "Shoot'em Up" defense sequence demanding instantaneous decimal-to-binary decryption. Operators must purge intruding data blocks by inputting their binary root values and discharging the logic cannon.
Escalation & Anomalies
Intrusion velocity escalates dynamically. Terminating 20 blocks elevates the threat level. The active logic gates scale from 3 (Level 1) to 7 (Level 13+), demanding raw calculation of masses up to 127.
System anomalies randomly manifest, yielding tactical advantages:
- Pulse Freeze: Suspends gravitational variables for 5 seconds, allowing the operator to purge swarms safely.
- Pulse Overclock: Initiates auto-targeting logic for 5 seconds.
- Pulse Cleaner: EMP detonation instantly purging a 3x3 sector.
- Pulse Touch: Bypasses the cannon, allowing manual touch-deletion of intruding blocks.
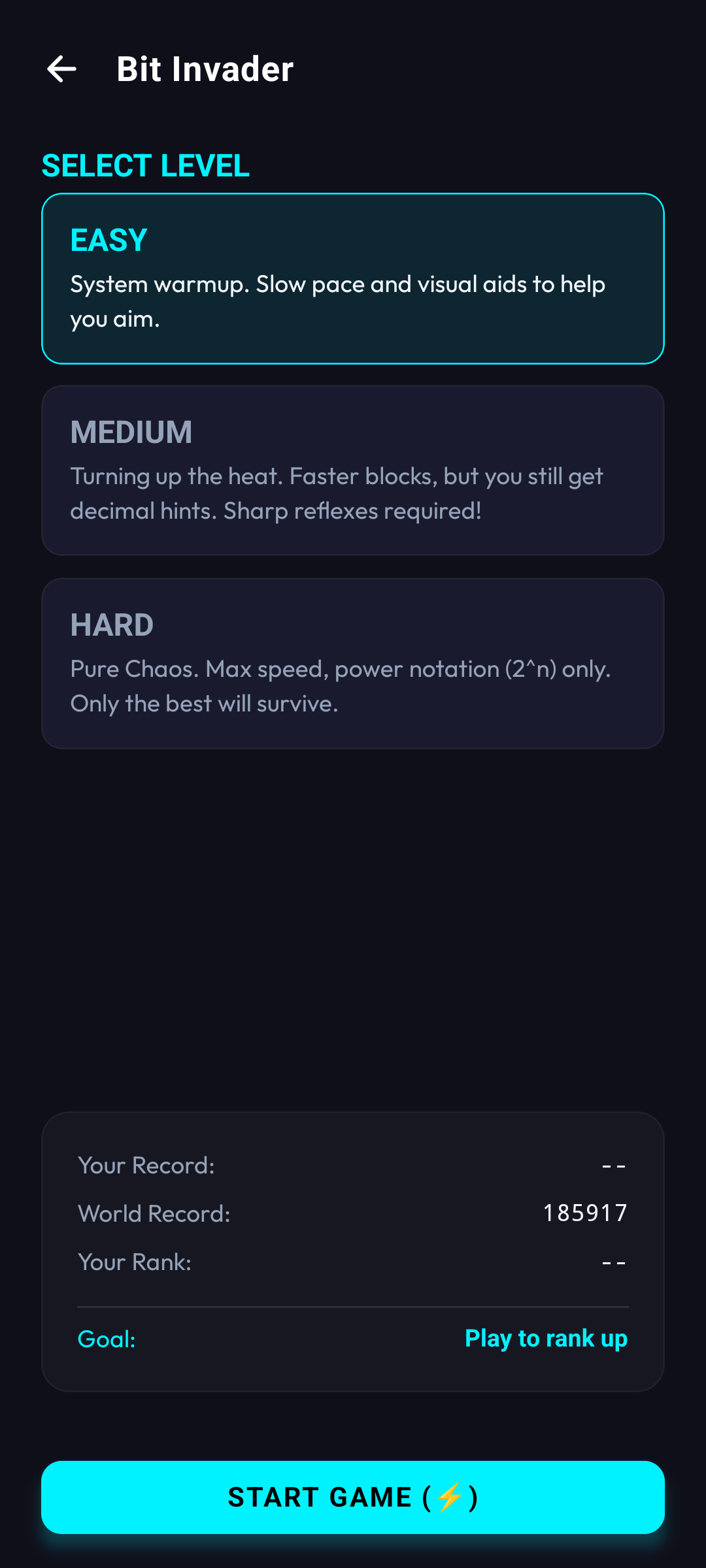
Invader Setup
Defense configuration parameters.
- Level configuration alters spawn & drop velocity.
- LEVEL 1: 2500ms spawn, 2000ms baseline drop.
- LEVEL 2: 2000ms spawn, 1500ms baseline drop.
- LEVEL 3: 1500ms spawn, 1000ms baseline drop.
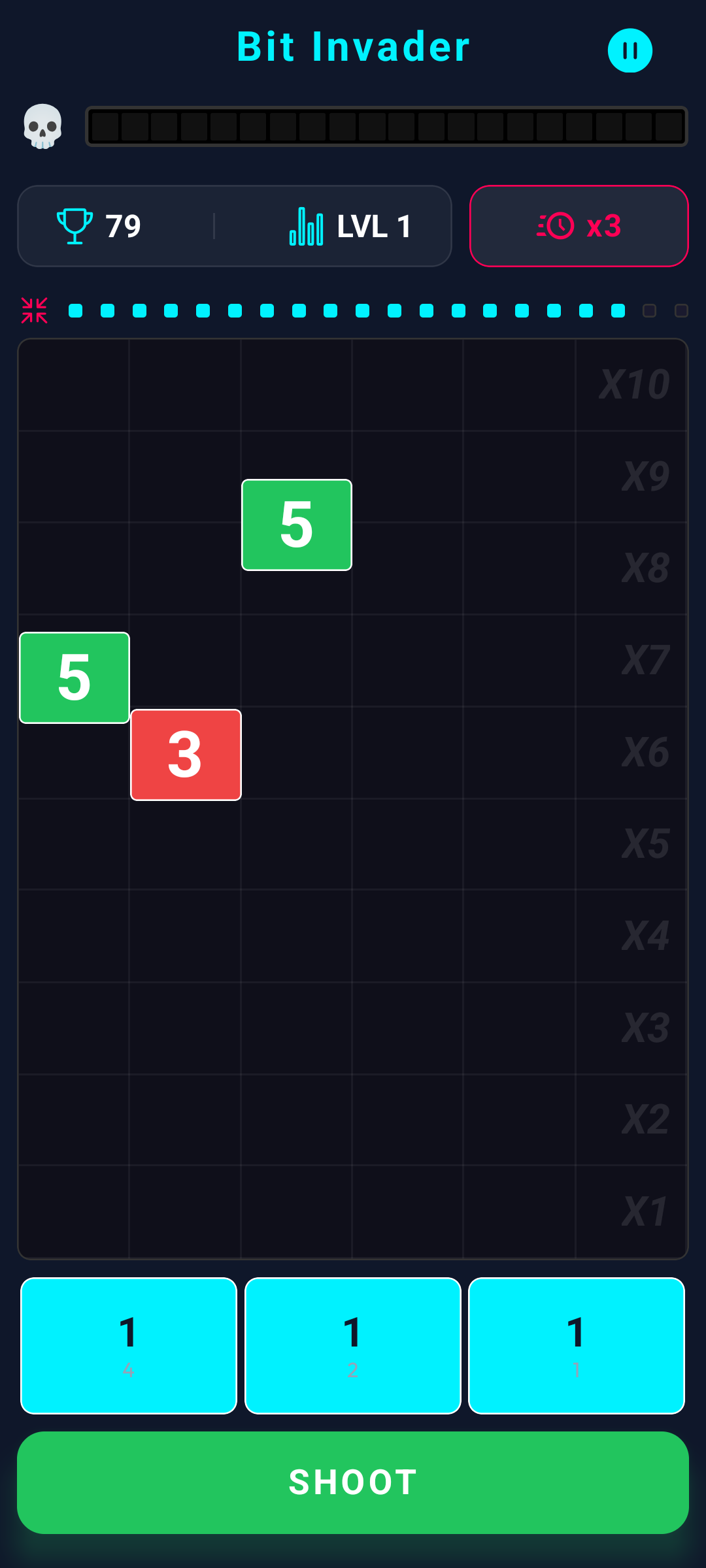
Standard Execution
Core defense loop.
- Input exact binary mass of the target.
- Discharge to terminate and extract score.
- 20 terminations escalates threat level.
- New logic gate engages every 3 levels.
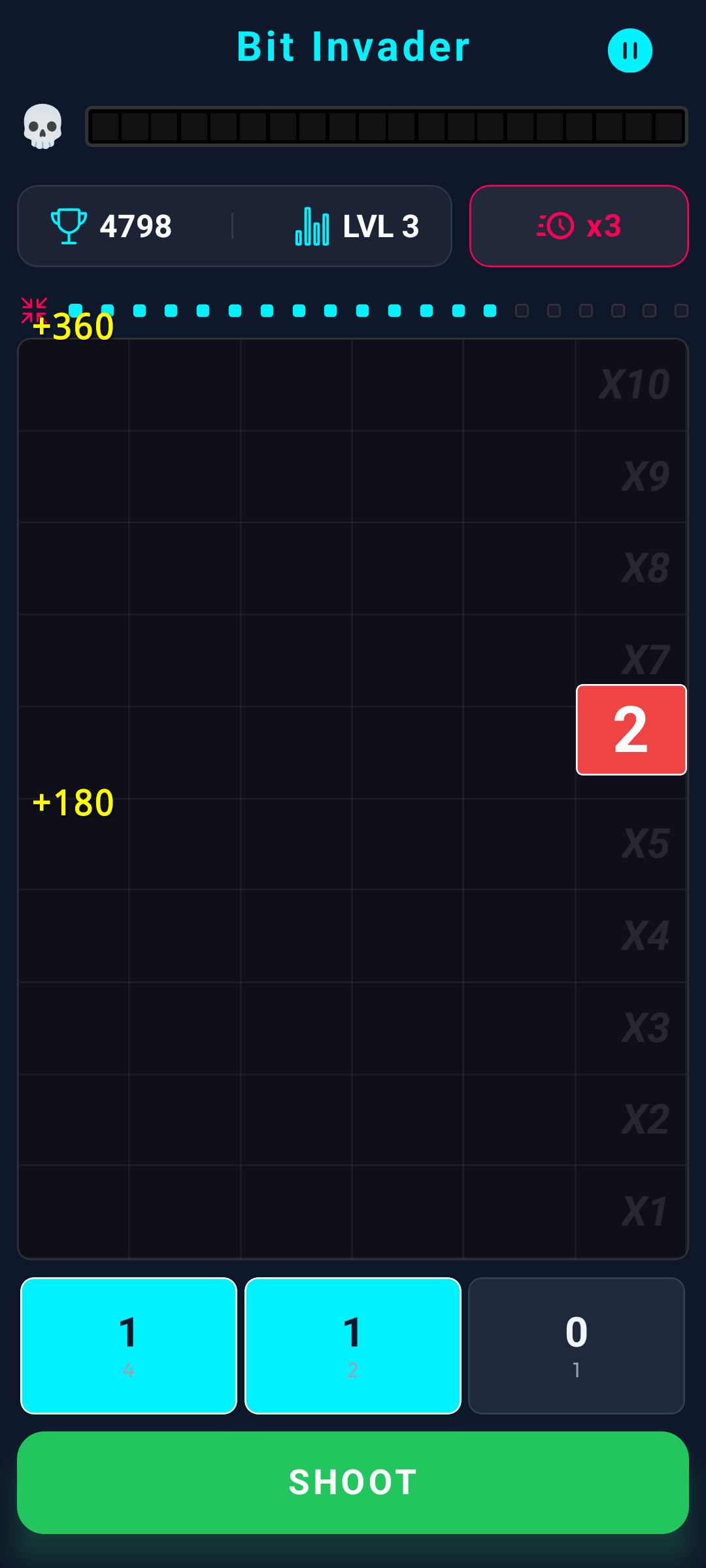
Yield Calculation
Data extraction mechanics.
- Altitude Bonus: Early interception = higher yield.
- Chain Bonus: Simultaneous terminations multiply score exponentially.
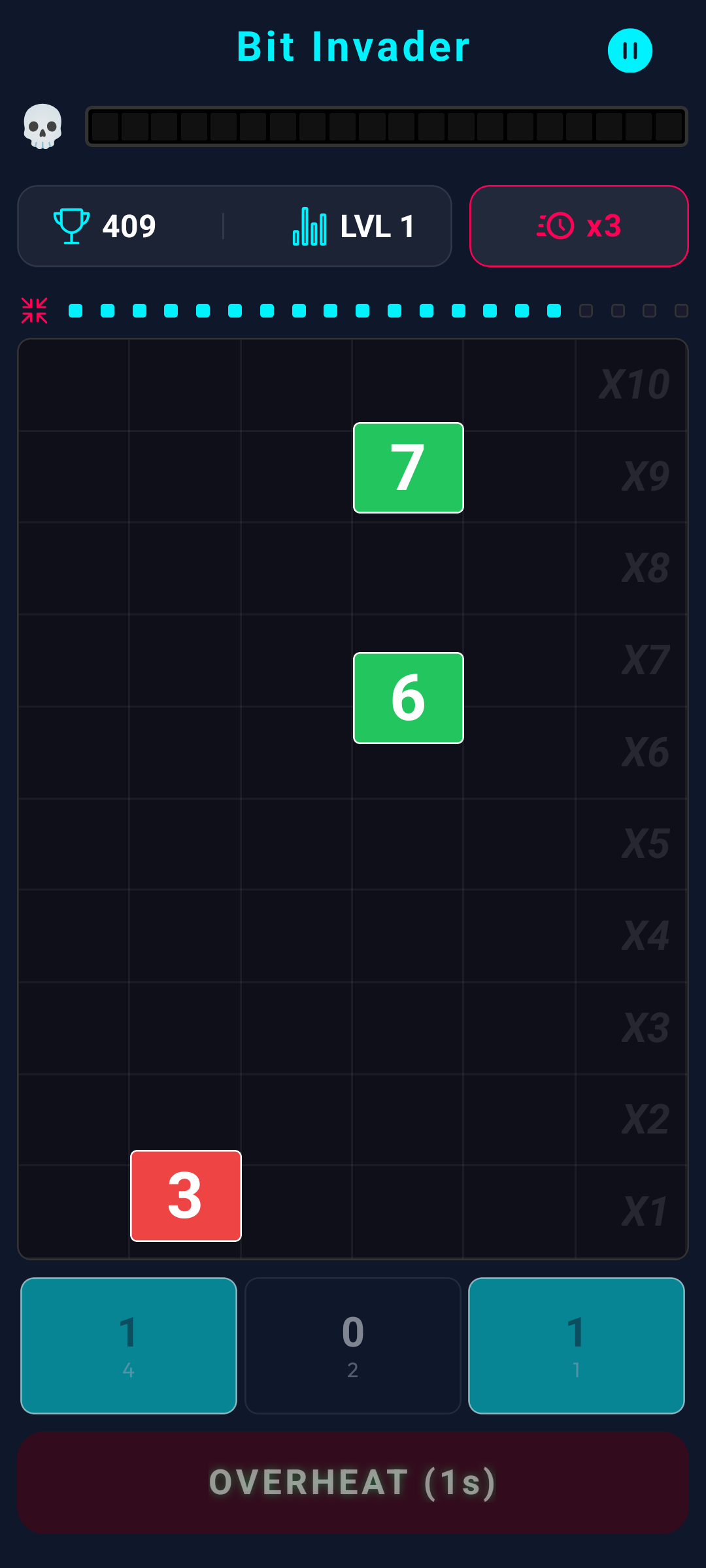
Overheat Consequence
Result of an invalid discharge.
- Discharging into the void jams the cannon.
- Lockdown: 1.0s to 2.0s depending on level.
- Creates lethal vulnerability against swarms.
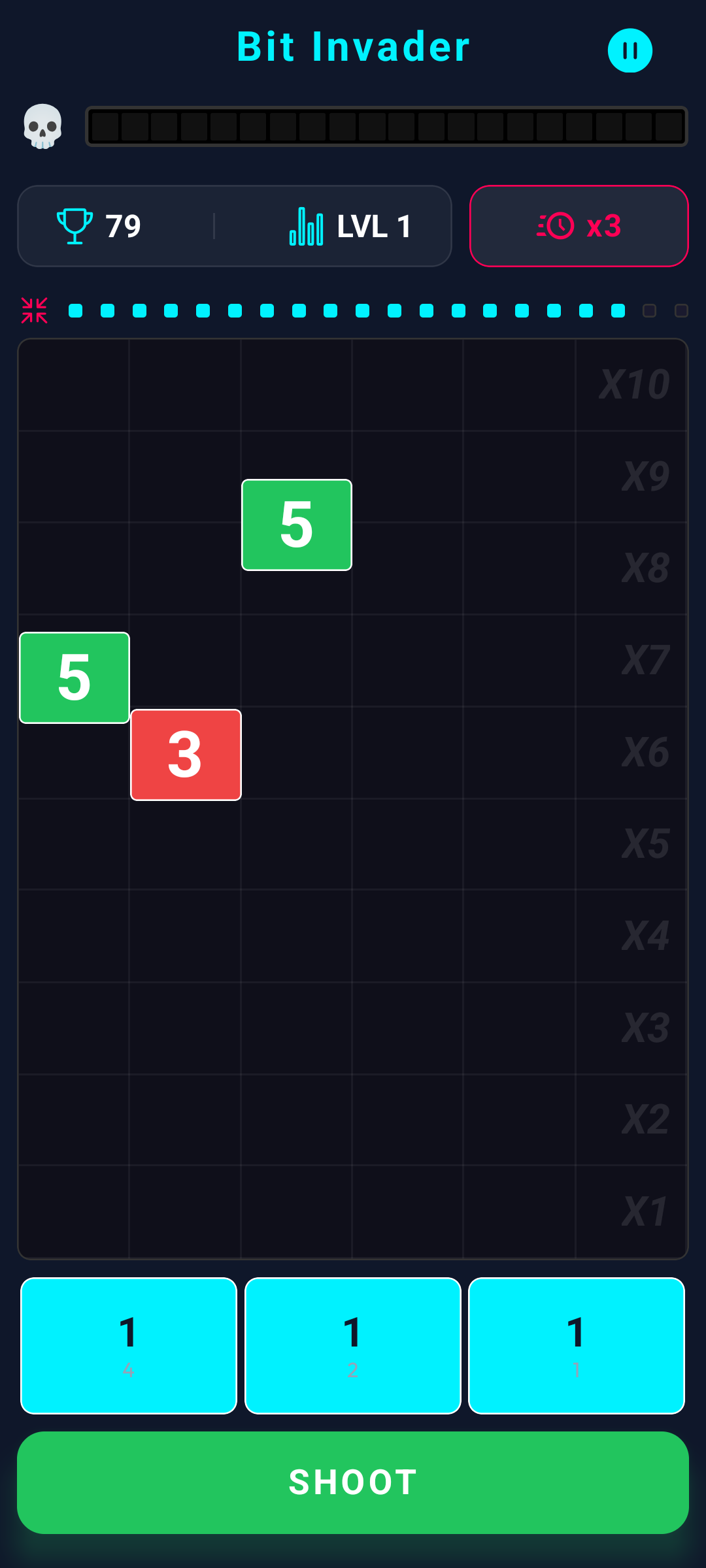
Pulse Anomaly
Rogue power-up injection.
- 10% probability of manifestation.
- Termination triggers hardware overrides.
- Also patches Core Integrity by 10%.
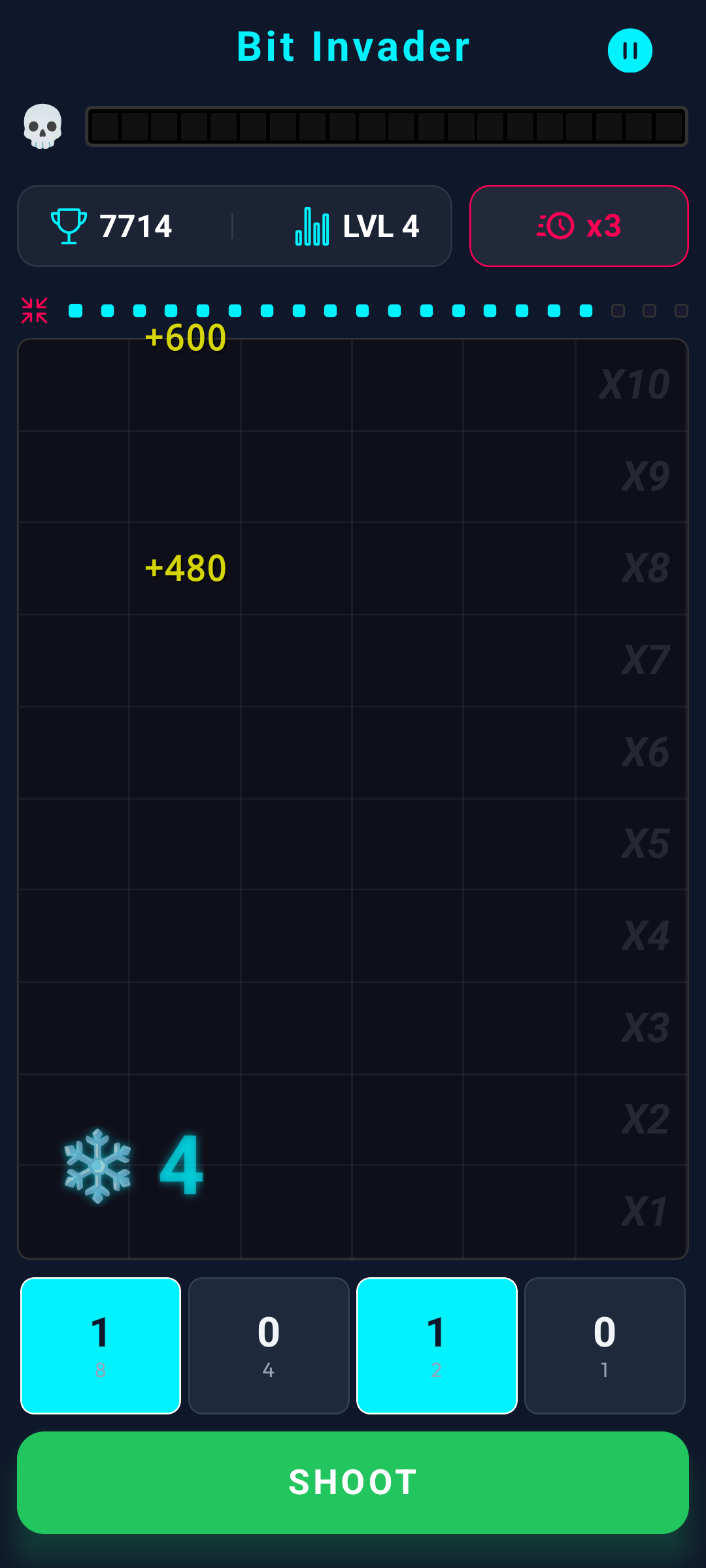
Anomaly HUD
Active override monitor.
- Chronological anomalies (Freeze, Overclock, Touch) display a counter in the lower-right node.
- Tracks remaining seconds of the active override.
- Irrelevant for instant-execution 'Cleaner'.
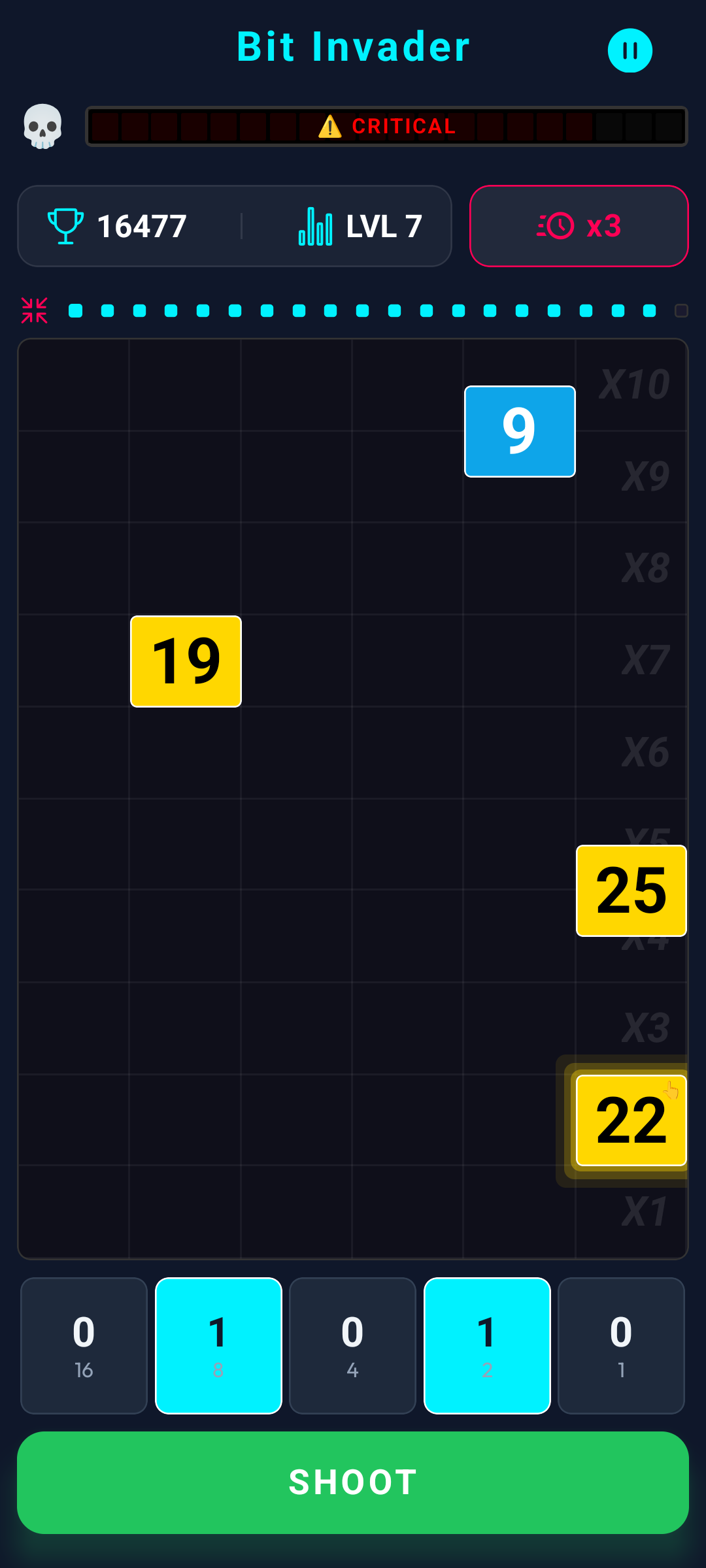
Integrity Warning
Structural damage monitor.
- Breaching targets deal 5-20% damage to Core.
- Null ('0') targets patch Core by 2%.
- Anomaly targets patch Core by 10%.
- 100% corruption = Terminal Shutdown.
Velocity Override
Speed & yield amplification.
- Toggle x1, x2, or x3 velocity via the chronos icon.
- Higher parameters multiply drop velocity and yield.
- Does NOT alter base spawn rates.
6. Universal Protocols: System Pause
To maintain execution integrity and block external algorithmic tampering (cheating), the mainframe permits only 2 secure suspension states per operation. Engaging a 3rd attempt flags the terminal—the sequence continues calculating in the background while the interface is obscured.
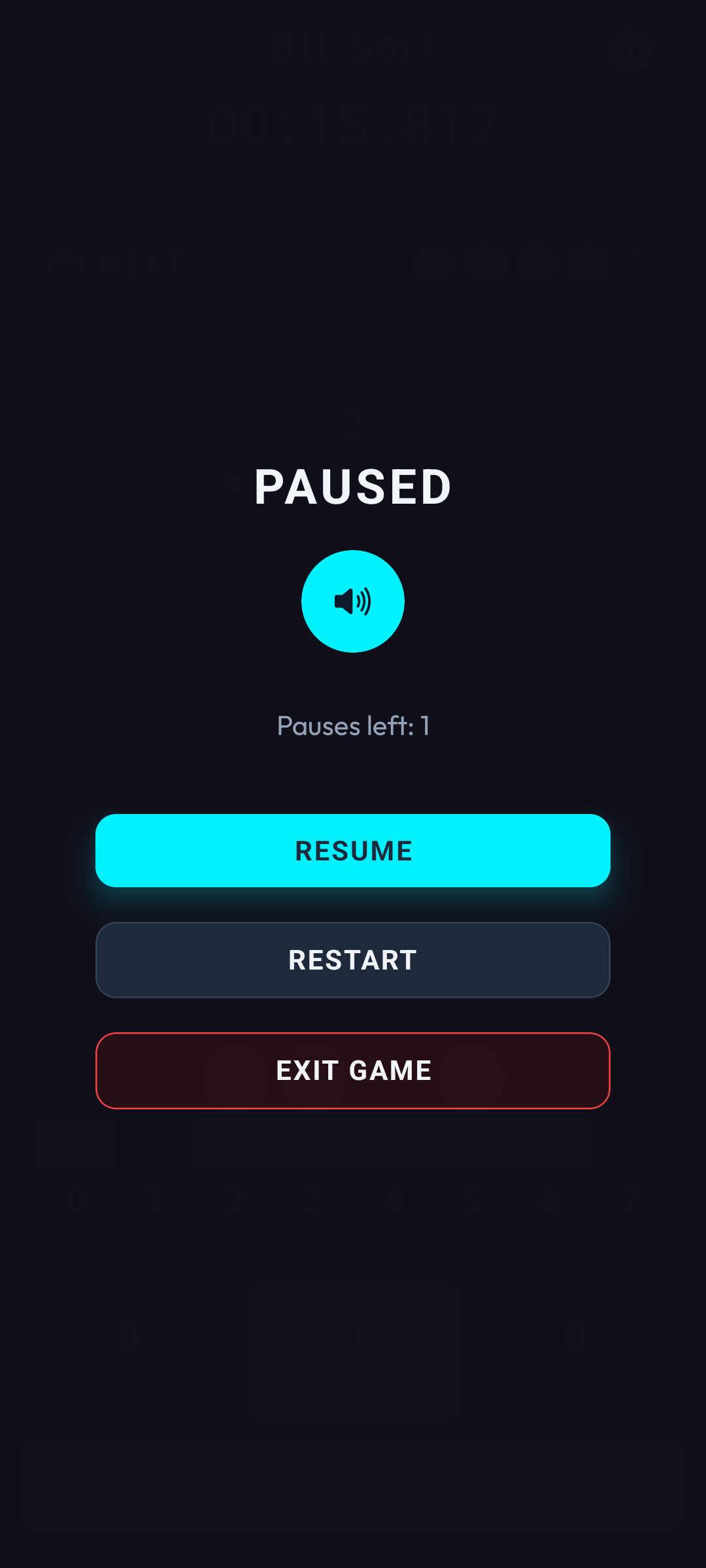
Secure Suspension
Execution halted by operator.
- Matrix is cloaked to block visual tampering.
- Strictly limited to 2 secure halts per cycle.
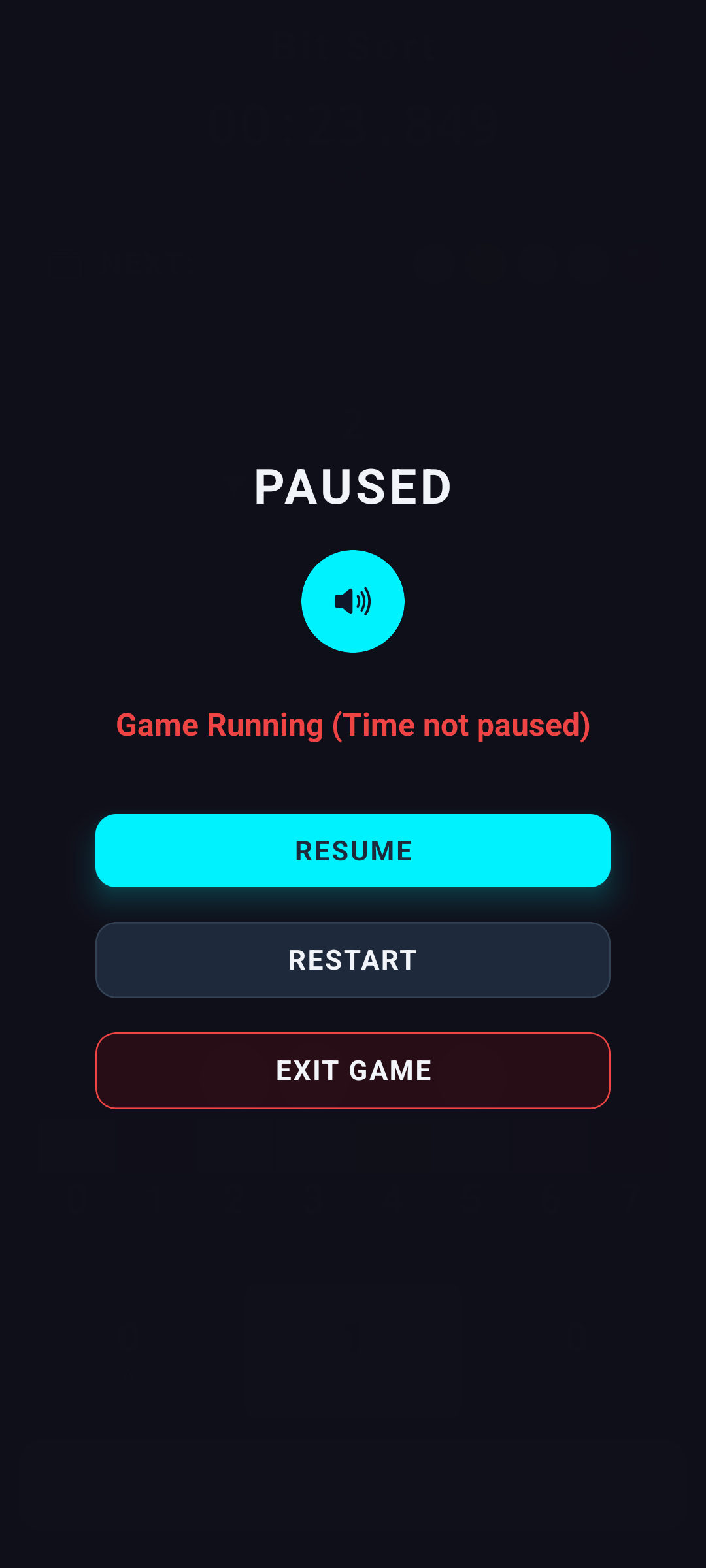
Anti-Tamper Protocol
Third halt attempt constraint.
- The sequence persists in the background memory.
- Chronometer runs, targets drop, penalties apply.
- Forces operators to execute or abort.
7. Simulation Environment
Simulation Mode guarantees operators are never completely locked out. When Energy depletes to 0, you can initiate fully functional practice sequences. While variables mirror live executions, any data generated (including Personal Bests or Network Records) is classified as void and not uploaded to the mainframe.
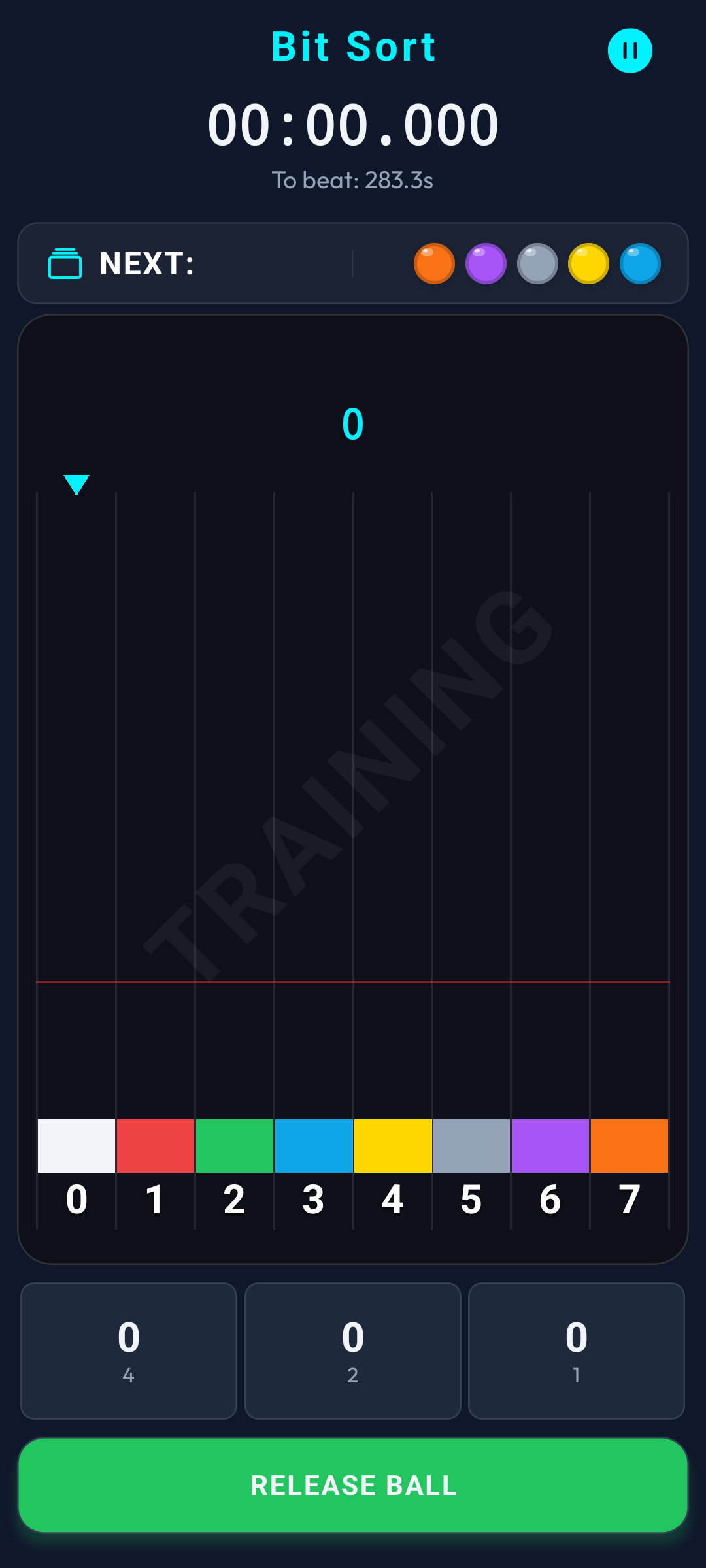
Bit Sort Simulation
Safe sandbox environment.
- Zero Energy consumption.
- Data is NOT synced to Global Rankings.
- Unlimited operational practice.
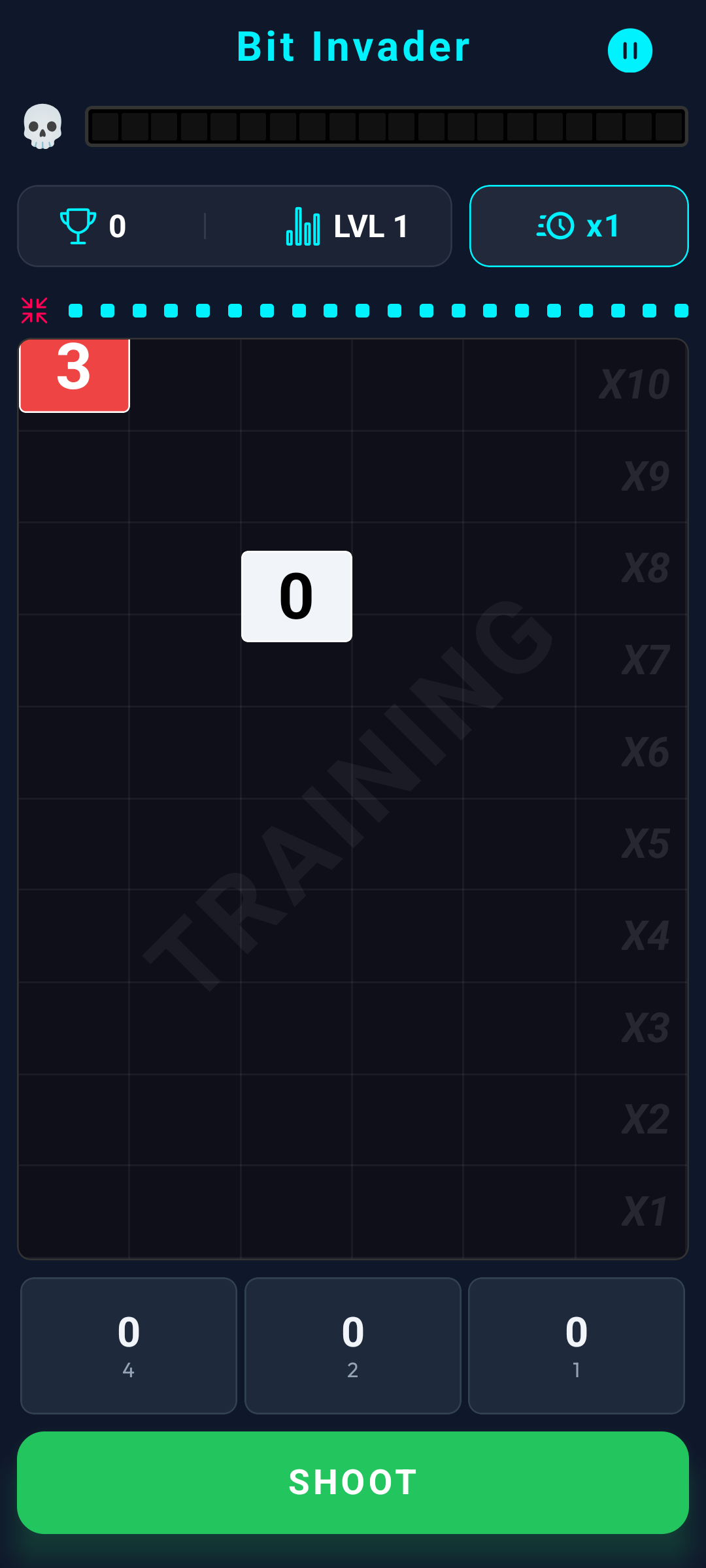
Bit Invader Simulation
Sandbox defense action.
- Standard execution rules enforced.
- Penalties activate but bypass global stats.
- Optimal for calibrating neural reflexes.
8. Global Network Rankings
Following termination of a live sequence, variables are compiled and logged. Operators can benchmark their telemetry against global network ranks across all tactical levels.
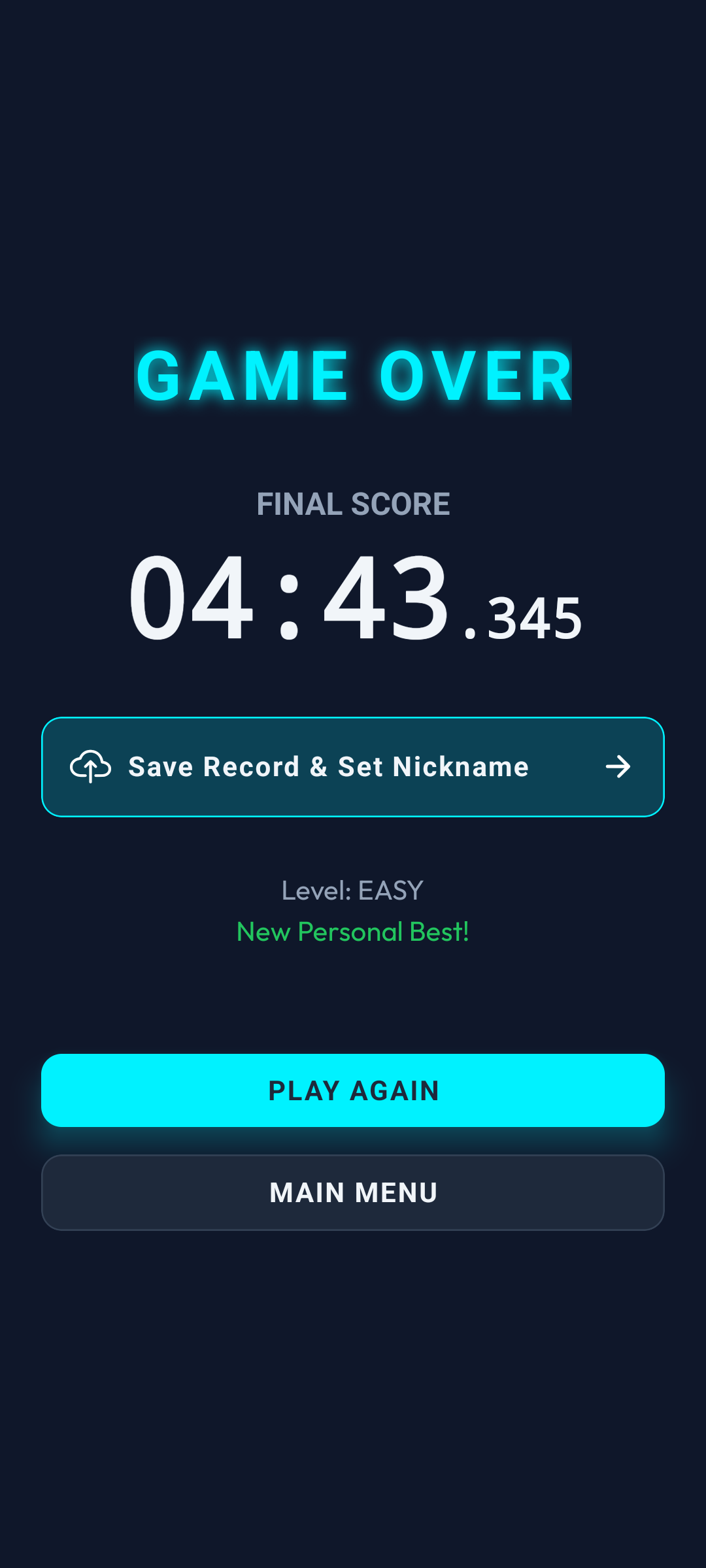
Data Logged
Post-execution analytics.
- Outputs final processed variables (score/time).
- Flags newly established Personal Bests.
- Prompts ghost profiles to uplink and secure data.

Network Leaderboard
Top 10 global operator signatures.
- Filters by Operation and Security Level.
- Integrates Report flag for corrupted callsigns.
- Sorts BitSort by Chrono (Ascending).
- Sorts BitInvader by Yield (Descending).
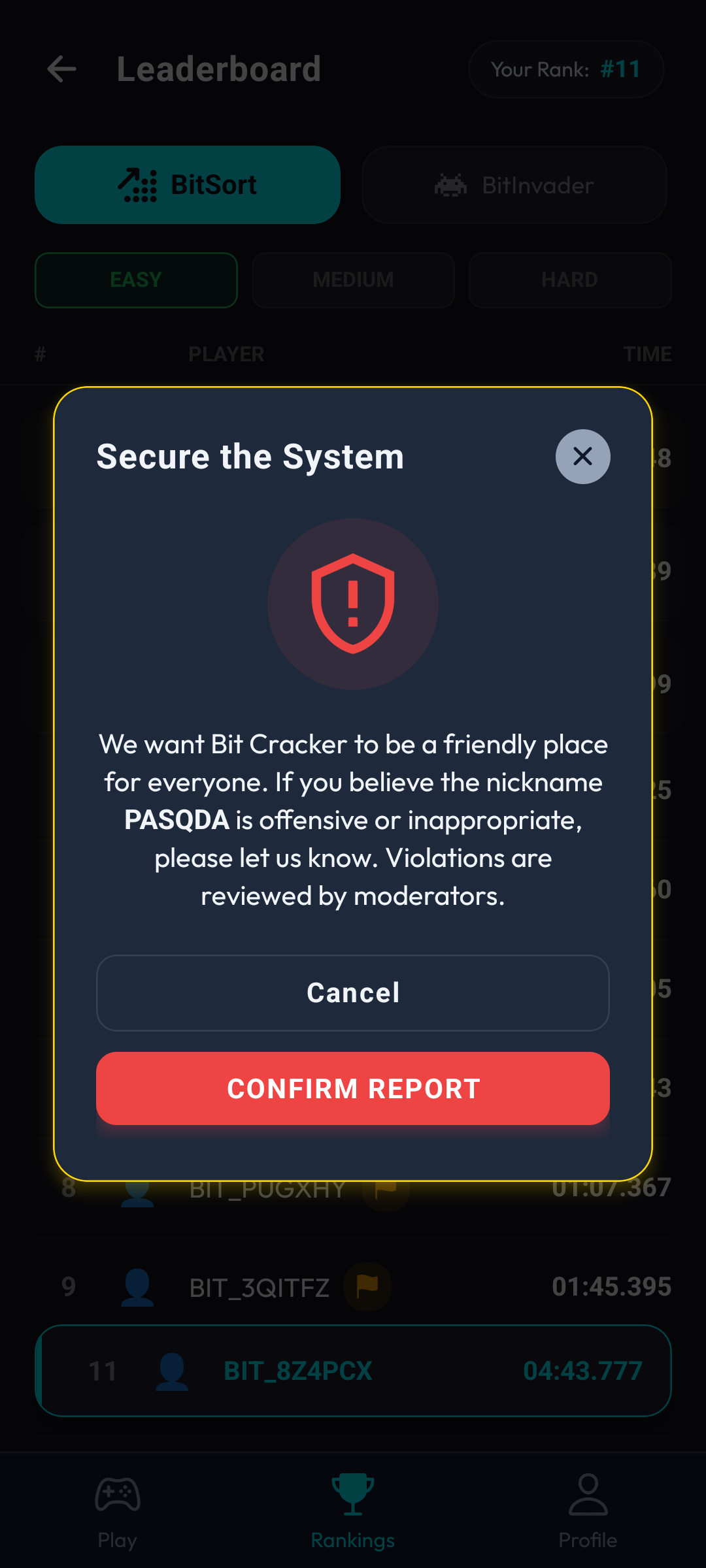
Purge Anomaly
Flag toxic or corrupted callsigns.

Rank Tracer
Sticky UI array implementation.
- Operators outside Top 10 are anchored at the bottom.
- Always outputs precise personal coordinates.
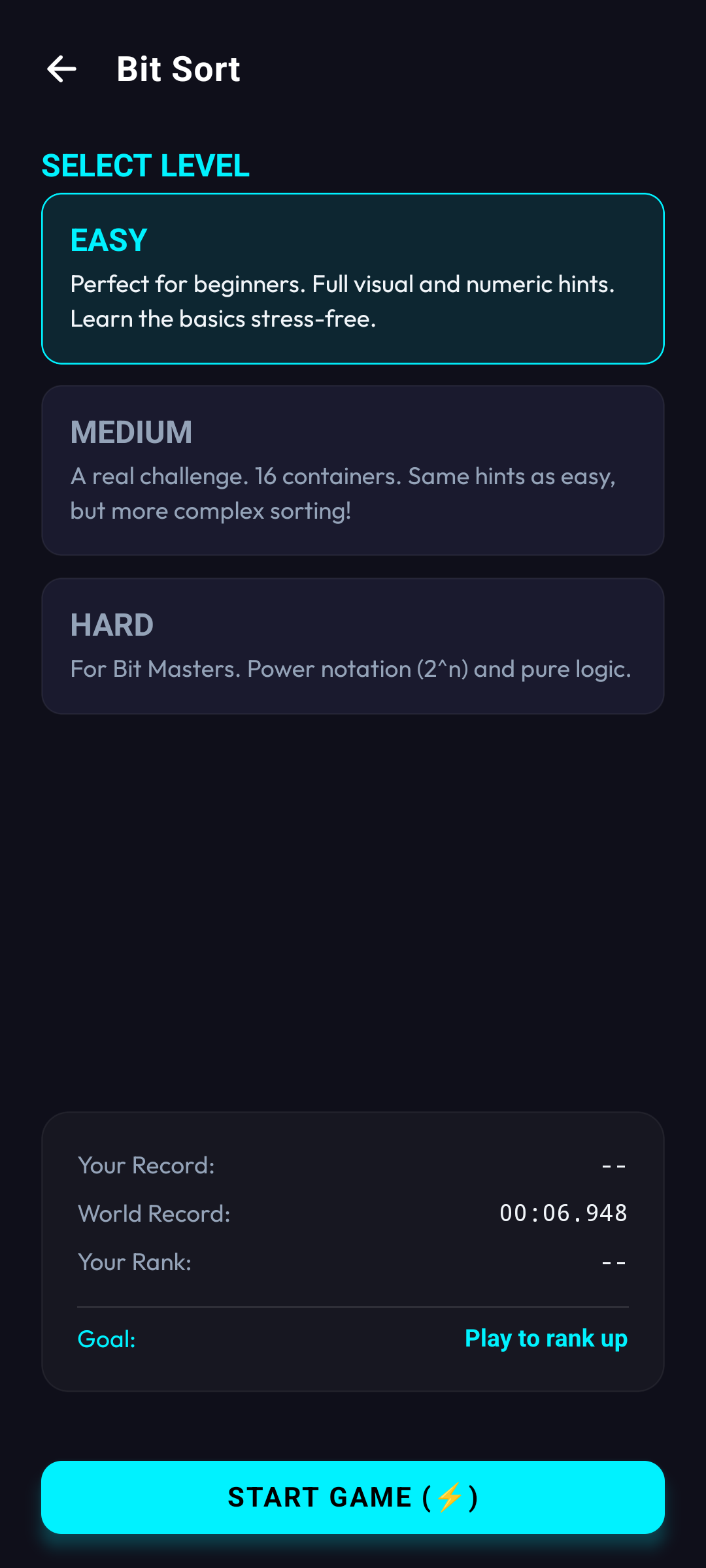
Pre-Execution Metrics
Setup matrix overlays.
- Displays Personal Best against the Global Record.
- Locks onto 'Rival Target' (next operator to overtake).
9. Operator Profiles & Configurations
Operators hold clearance to alter terminal settings, extract detailed performance matrices, switch uplink credentials, and rewrite their callsigns.
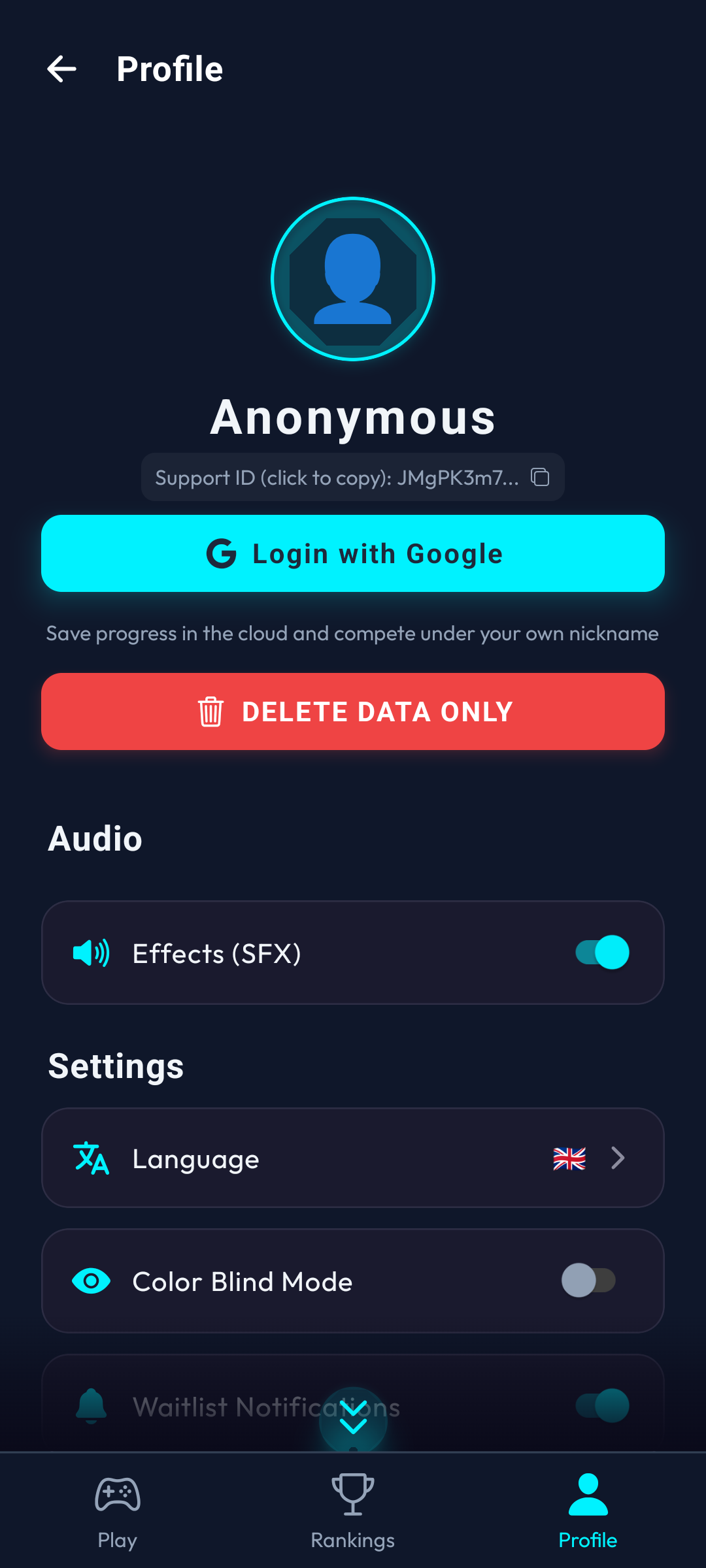
Operator Identity Hub
Core configuration settings.
- Outputs initialization timestamp & variables.
- Overrides for SFX, Synth Music, and Visual Impairment mode.
- Visual Impairment shifts terminal colors for color blind operators.
- Global Node (Google Account) uplink portal.
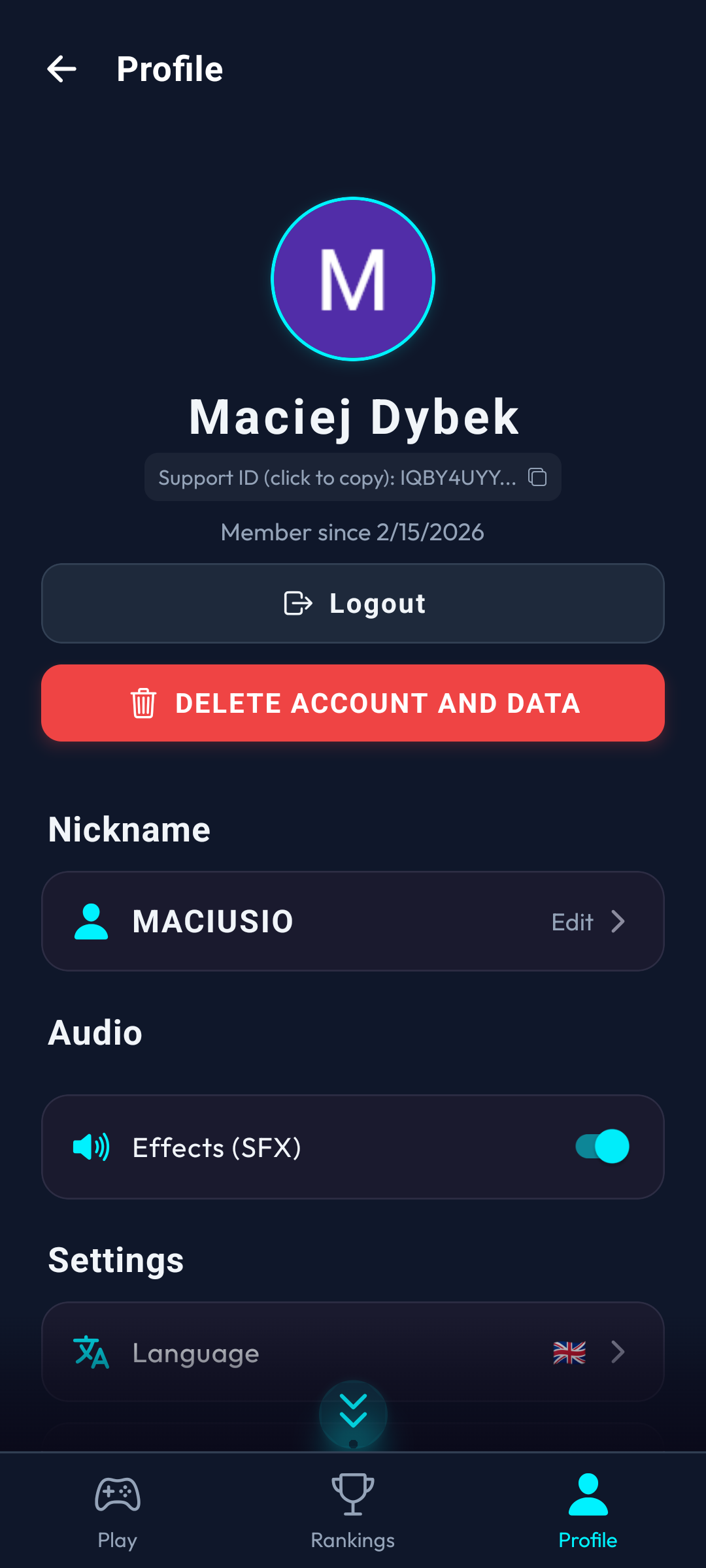
Ghost Profile
Offline, untraceable state.
- Data strictly bound to local hardware.
- Hardware loss = permanent data deletion.
- Uplink required to push data to the mainframe cloud.
- Unlocks Callsign modification protocols.
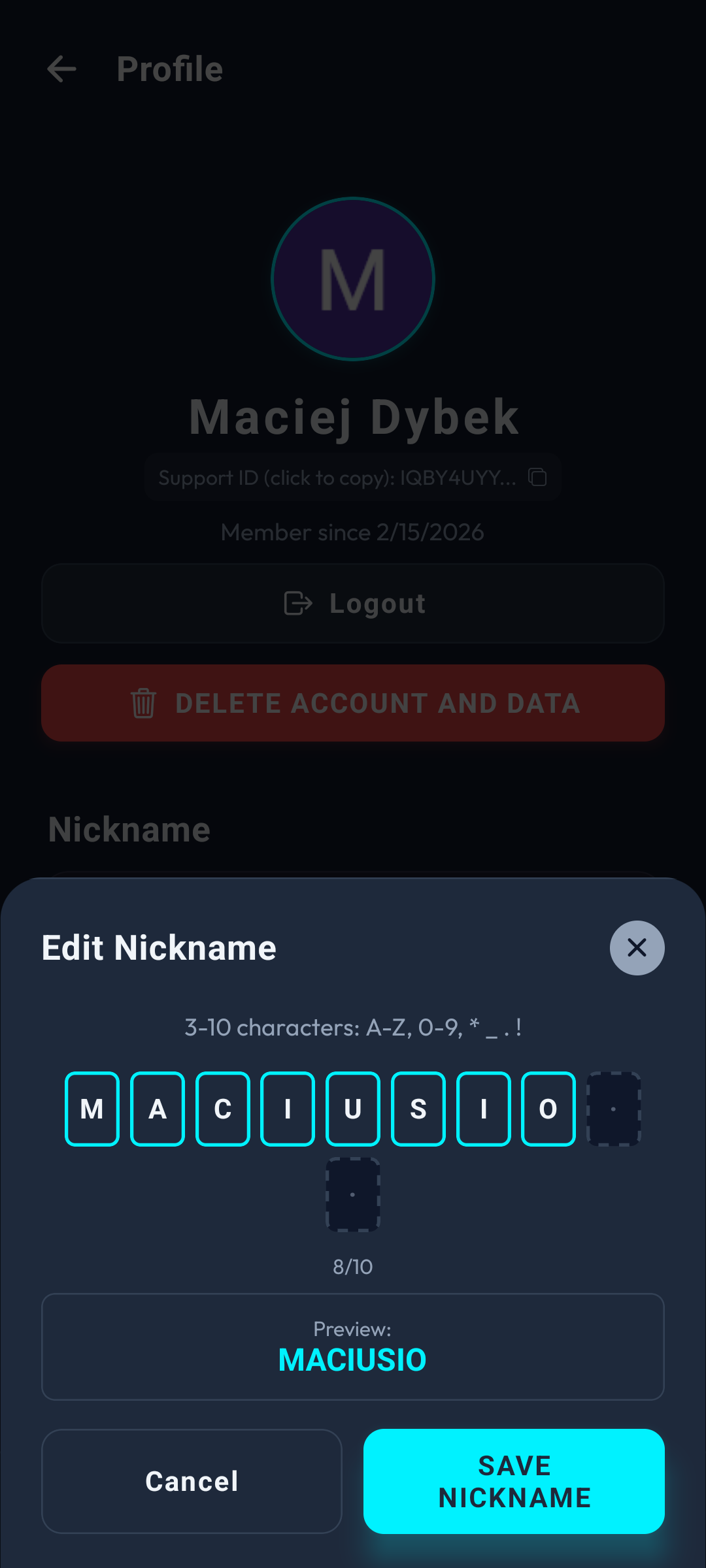
Callsign Override
Network identity editor.
- Parameter: 3-10 authorized characters.
- Pushes instantly to all global arrays.
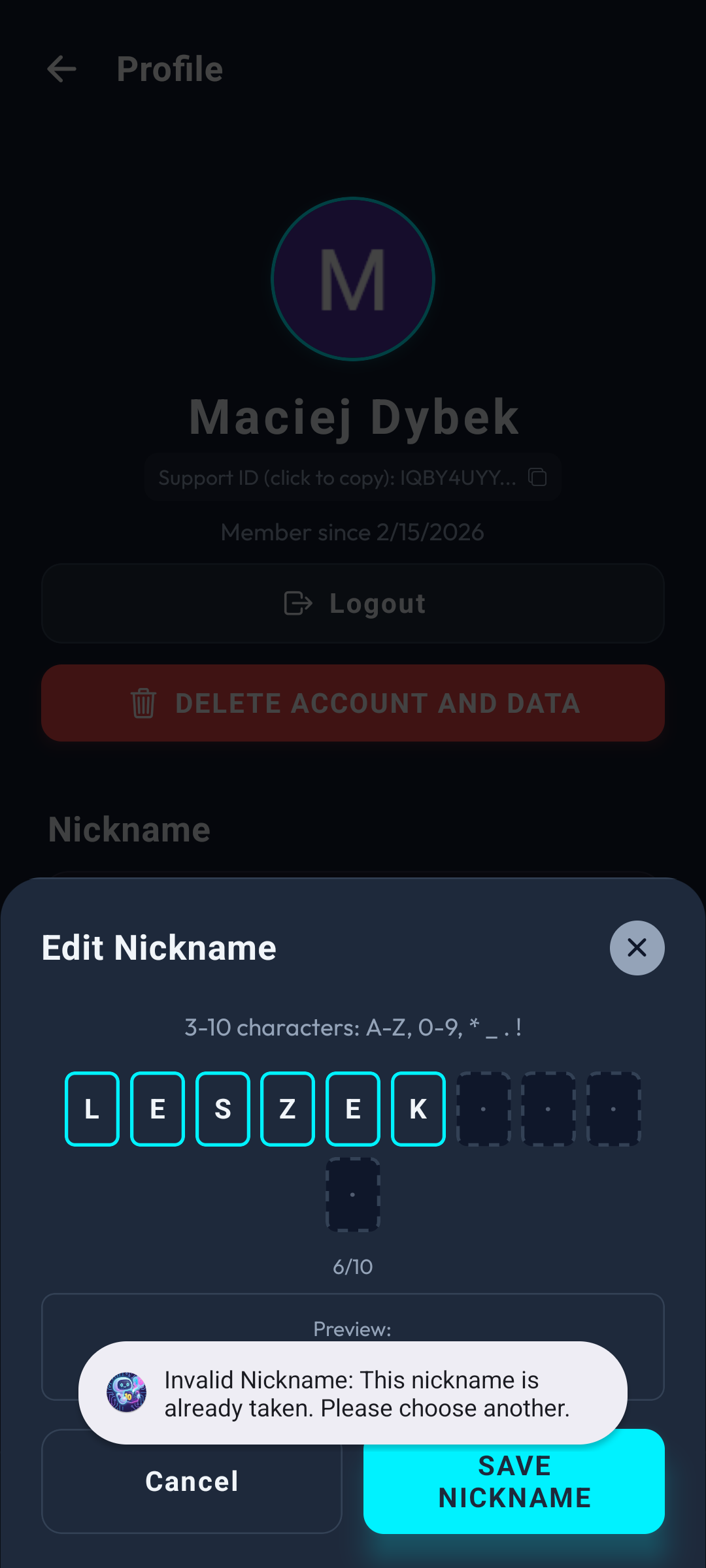
Validation Rejected
Callsign constraint firewall.
- Scans global network for duplicates.
- Blocks unauthorized string characters.
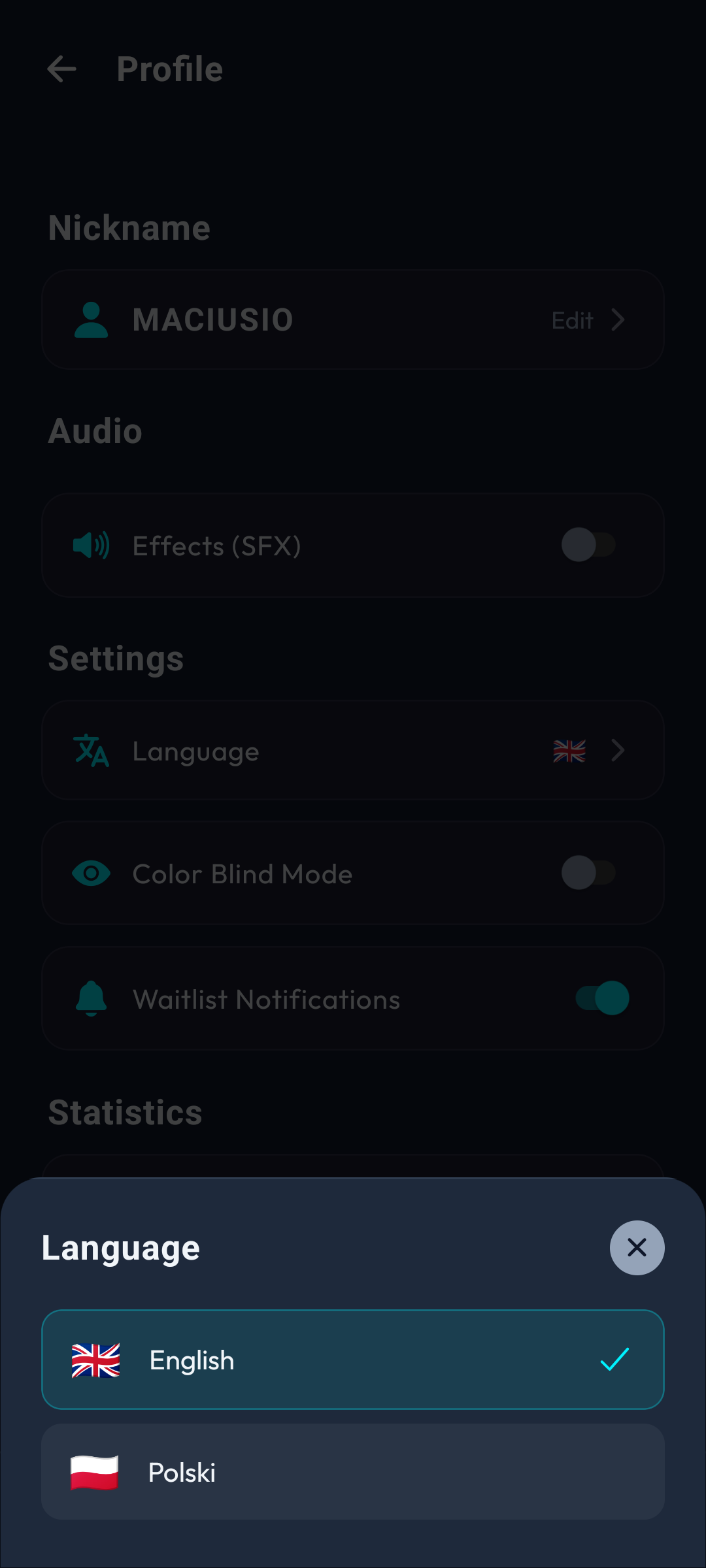
Linguistic Protocols
i18n translation matrix.
- Currently supports EN / PL linguistic nodes.
- Future syntax packs pending.
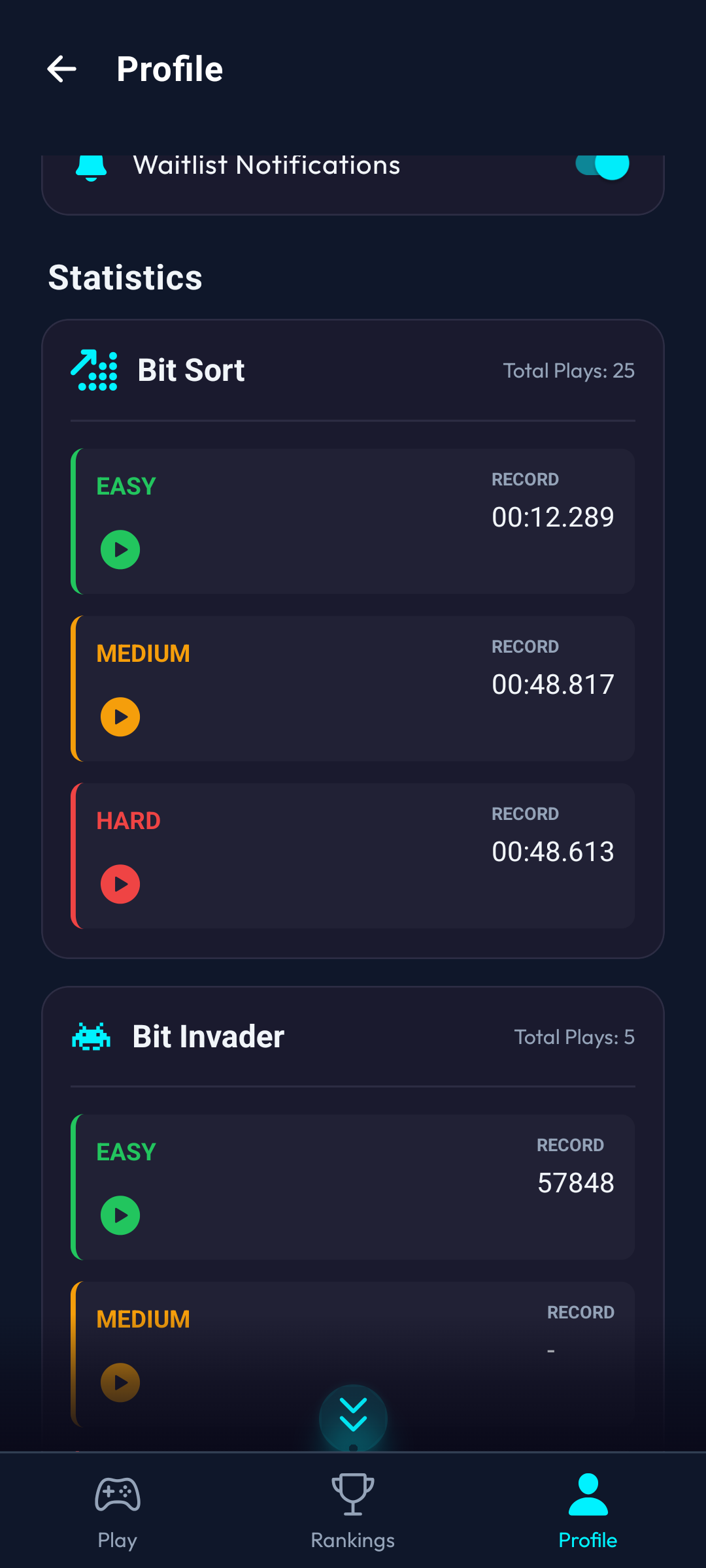
Telemetry Logs
Extracted operator data.
- Centralized repository of all variables.
- Quick-boot 'Execute' switch for every parameter.
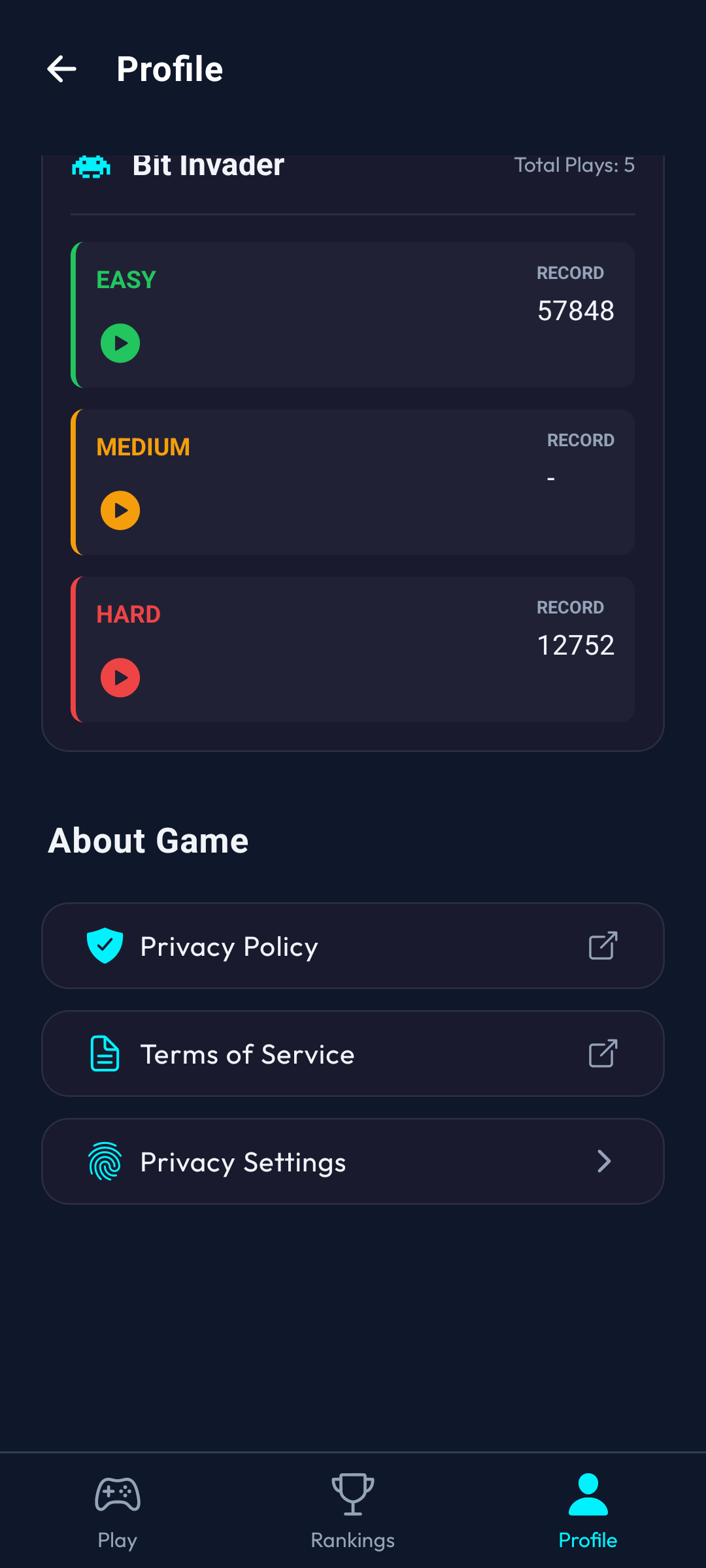
Legal & Support Firewalls
Network compliance data.
- Access port to all corporate policies.
- Reconfigure your tracking firewalls.
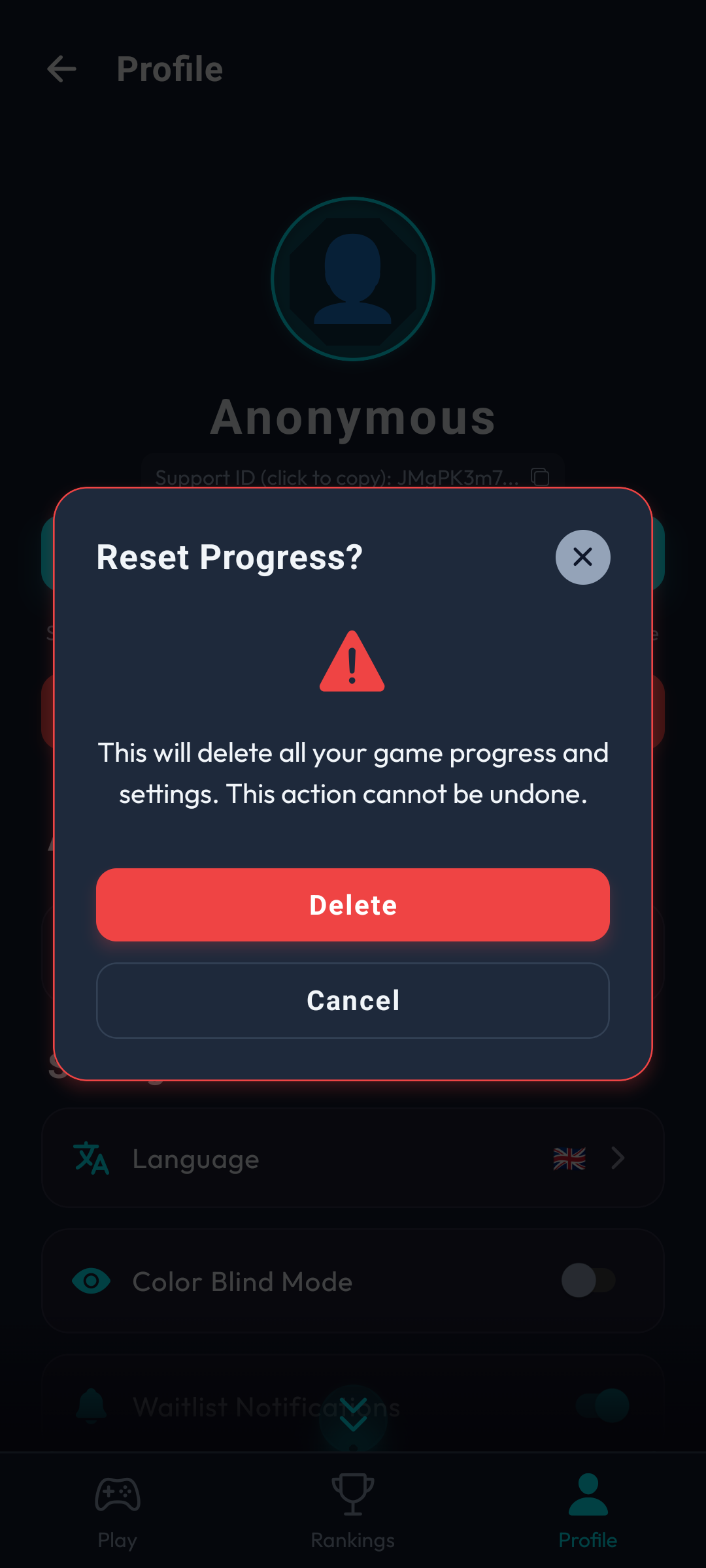
Terminal Purge
Complete profile erasure.
- Shreds all local telemetry and network ranks.
- Severs push notification uplinks.
- Forces a log-out from the Global Node.
10. Mainframe Administration
Global architectures occasionally enter maintenance cycles requiring operator standby or deployment waitlists. The system includes fail-safes for critical terminal errors.
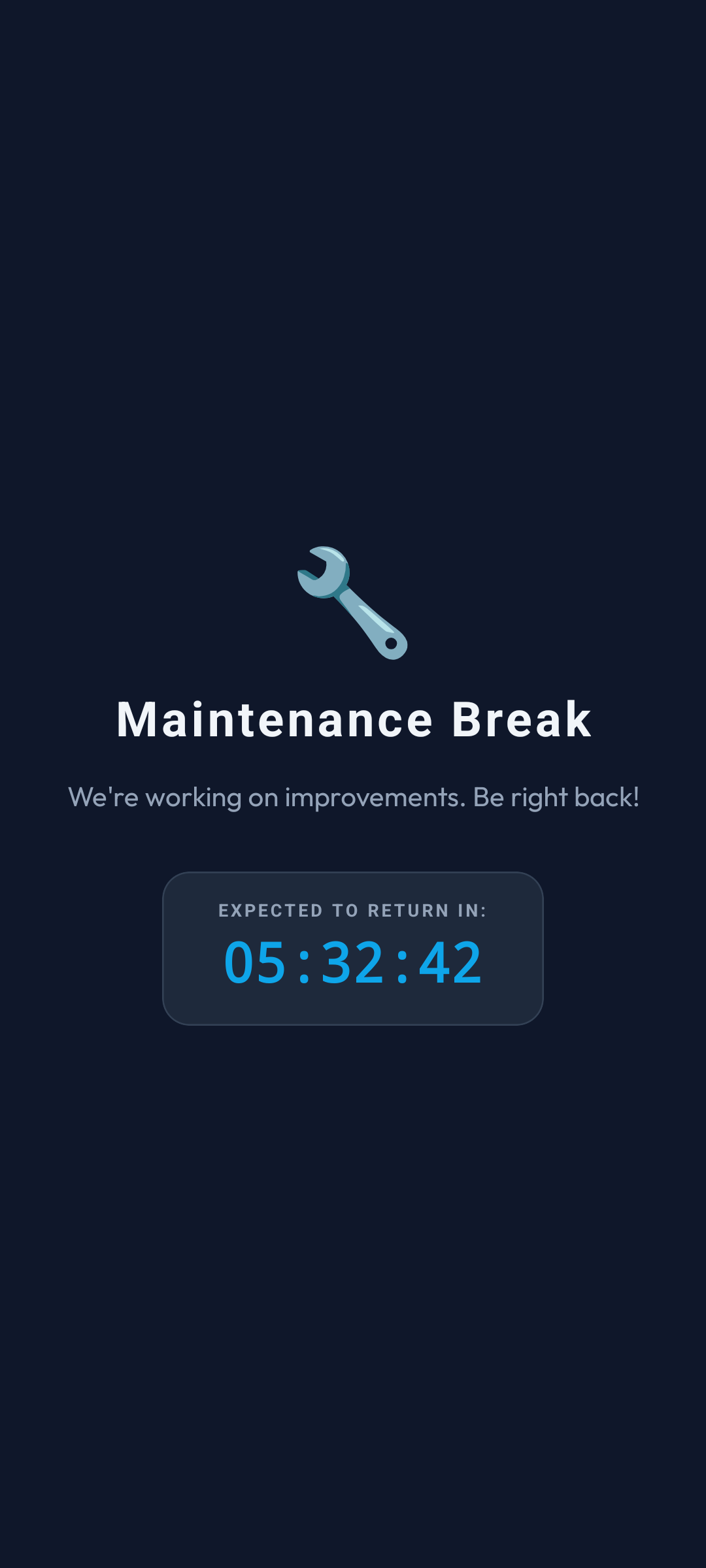
Maintenance Terminal
Mainframe temporarily offline.
- Core servers are undergoing recalibration.
- Blocks all interaction overlaying App.tsx.
- Outputs a dynamic chronometer to network reboot.
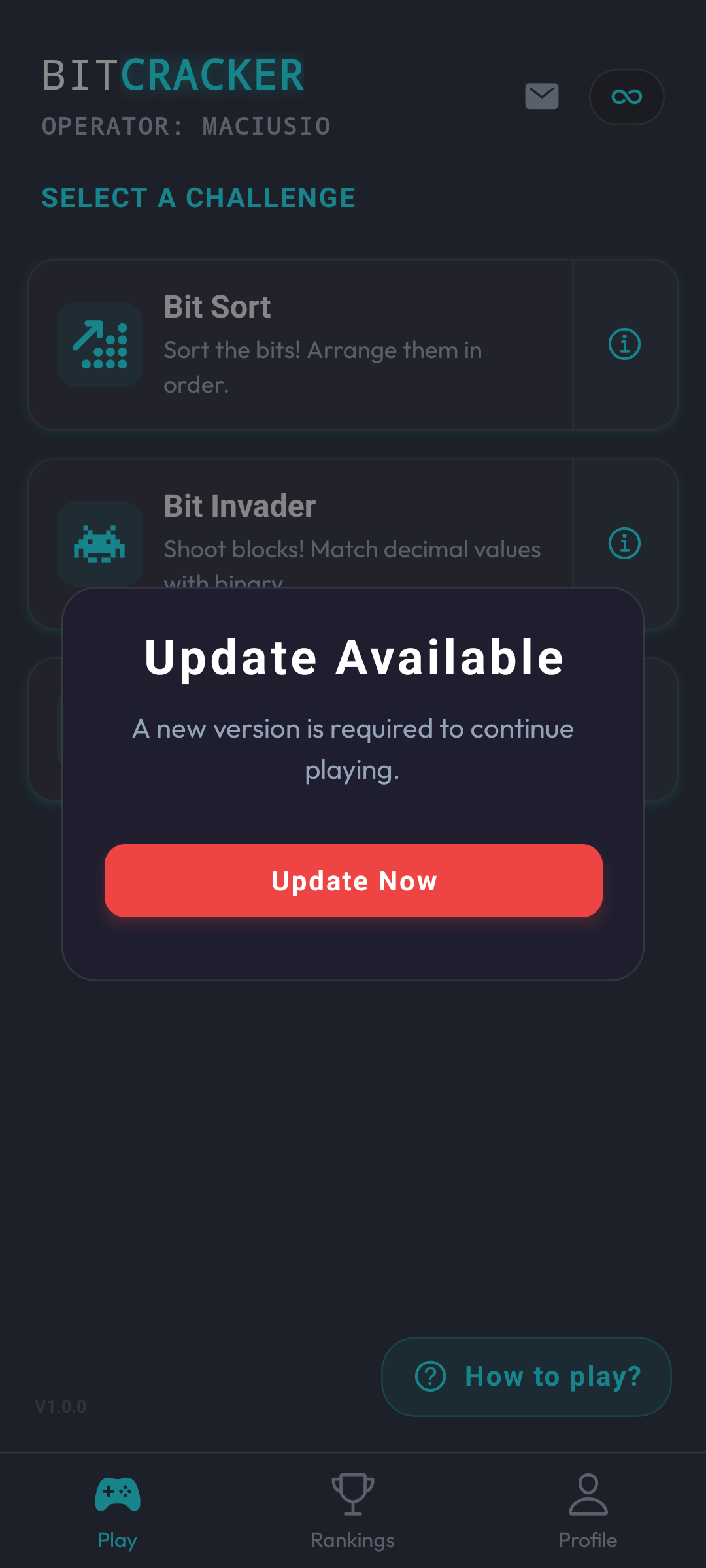
Hard Sync Guard
Mandatory version synchronization.
- Locks all executions until the terminal is patched.
- Guarantees handshake compatibility with the cloud.
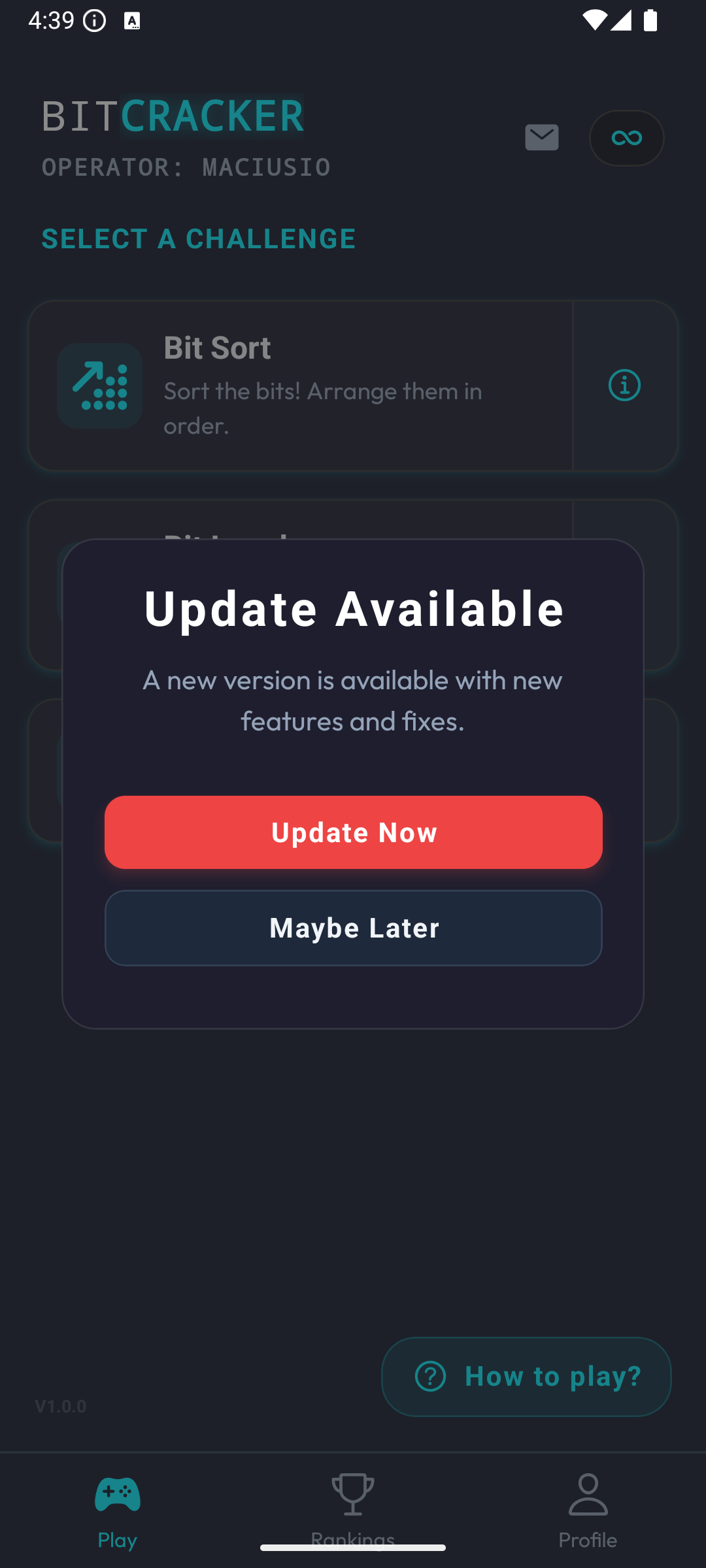
Soft Sync Notice
New terminal assets detected on the network.
- Non-intrusive package notification.
- Permits continued operations on legacy builds.
- Can be dismissed until the next boot sequence.
Terminal Error
Global error boundary fail-safe.
- Isolates unhandled logic anomalies (JS exceptions).
- Forces a safe terminal reboot sequence.
- Prevents total hardware crash.